GSM Bug. Sounds A Bit Scary, Doesn’t It?

Is it detrimental to your personal health? No, but it is detrimental to your personal privacy. GSM (Global System for Mobile) bugs are covert listening devices that can be accessed and controlled from almost anywhere in the world.
But what makes these sneaky little monsters particularly concerning is both their accessibility and their real-world applications. Because they’re not just fancy gadgets you only see in movies or on TV.
They’re very real. And when used properly, they can wreak havoc in both your personal and professional lives.
Keep reading to learn more about how these wireless listening devices work, where they’re found, and what steps you can take to protect yourself and your business.
How a GSM Bug Works
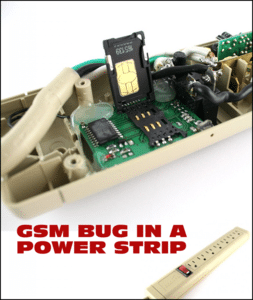
Think of a GSM bug as a stripped-down cell phone. No keypad. No speaker. No screen. It is just a transmitter, a microphone, usually a battery, and sometimes a miniature video camera. Just add a SIM card, and this electronic eavesdropping device is ready to spy.
The important thing to know is that a GSM bug leverages the power of the international cellular telephone system. The bugger can listen-in, and even watch if video-equipped, from anywhere there is cellular phone service.
Activation features can be extensive. Basically, all device types can be activated by calling the phone number associated with the device’s SIM card. Some can automatically alert the eavesdropper when they sense sound in the area, motion near the device, or movement of the device itself, as when it is used in a vehicle.
GSM Bug Types
There are several models of GSM bugs. The most common ones being sold have a self-contained battery. These are used as temporary, quick-plant eavesdropping devices.
Other models are made for permanent placement. Placements and disguises seem to be limited only by imagination. You can find them in motor vehicles, desk phones, speakerphones, and power strips. Anything which has its own power source can also power a GSM bug—indefinitely.
GSM Bug Special Features

As we discuss the specifics of these wireless listening devices, it’s easy to fall into the trap of thinking they only pick up specific conversations. But their capabilities range, and a more sophisticated GSM bug might come with some or all of these additional features:
- The ability to take still photos when triggered via SMS and send them as MMS messages.
- Standby time of 12-15 days, with a working time of 3-5 days.
- Recording of audio and video to an internal SD memory card.
- Reporting of GPS location upon receipt of an SMS order.
- Infrared motion detection.
- A listening range of 30-50 ft.
GSM Bug Price & Availability
It wasn’t that long ago when listening devices of this type were only available to governments and law enforcement, at the cost of thousands of dollars. Times have changed, dramatically.
A GSM bug can now be purchased on the Internet. Outlets include eBay, Alibaba, Amazon, hundreds of “spy shops,” and even through the Walmart website. Anyone with access to the Internet, and approximately $10 to $30 dollars, can now spy like the professionals. And they do.

How Many GSM Bugs Are Out There?
GSM bugs first made news in 2007, which makes an exact estimate almost impossible.
While there is no definitive count on the number of GSM bugs manufactured and sold, one manufacturer on Alibaba says they can ship 10,000 listening devices each month.
Doing the math at 10,000 bugs per month, that’s about 1,320,000 bugs, just from one factory in China. The list of manufacturers on Alibaba alone seems endless, and there are other manufacturers worldwide.
Is a GSM Bug Listening to You?
Chances are, you live your life like most of us. You work hard, you love your family, and you spend your free time pursuing other interests and hobbies—like watching Netflix. So it’s probably weird to think anyone would ever plant a listening device in your living room. But the reality is, the reasons an eavesdropper might invade your privacy are vast and varied.
If any of the following circumstances or characteristics apply to you, you’ll want to take steps to protect yourself:
- An active romantic relationship.
 A dying romantic relationship.
A dying romantic relationship.- A wishful romantic relationship. (stalker)
- Your inherent appeal to a voyeur.
- A lawsuit.
- Anything to do with business competitiveness.
- Celebrity status.
- Merger and acquisition activity.
- Co-worker competition.
- Target of activists.
- Anything to do with politics.
- Nosy neighbors.
- Special intellectual property knowledge.
- New business venture.
- Blackmail potential.
- Revenge.
- An adverse publicity potential.
- Boardroom strategies.
- Knowledge of trade secrets.
How to Find a Covert GSM Bug

Finding a GSM bug is not easy without the proper instrumentation and knowledge of how to use it. GSM bugs spend most of their lives in an inactive state.
If you are a private individual, you may want to start your education by reading Eavesdropping Snoops – The Average Person’s Guide to Stopping Them.
If your situation is business-related, start by reading Corporate Bug Sweep | TSCM Methodology, Corporate Counterespionage Strategy, and Executive Suite Security Considerations for Information Security and Operational Privacy.
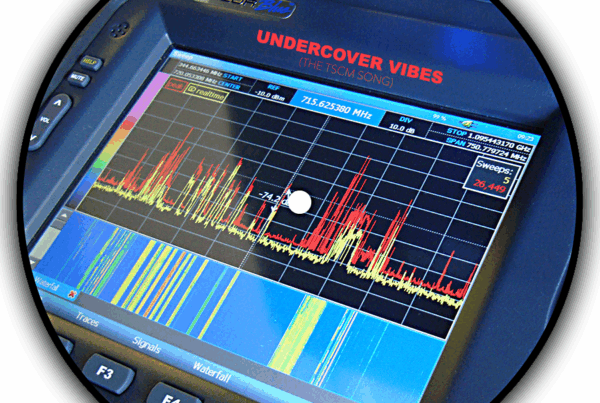
There are some high-end GSM bug detection instruments made by companies like shearwatertscm.com, bvsystems.com, and intpro.co.uk. Low-end gadgets are sold as well, but their effectiveness is questionable, and the range of possible eavesdropping techniques they may detect is limited.
In either case, a do-it-yourself bug sweep with high-end instruments, or low-end gadgets isn’t advisable or cost-effective. Help from a Technical Surveillance Countermeasures (TSCM) specialist is your next best step. Read How to Choose a Competent TSCM (Technical Surveillance Countermeasures) Consultant, or contact us directly with your questions, or a request for a referral.
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.


 A dying romantic relationship.
A dying romantic relationship.