How to Choose a Competent TSCM / Counterespionage Consultant

Organizations need competent Technical Security Consultants (TSCM) to protect them from espionage. However, many first-time users don’t know how to find a consultant or what they should expect for their money. Follow these tips for an instant education.
Tip #1 – Nine out of ten TSCM techs did not graduate in the top 10% of their class.
In your search for a competent TSCM consultant you’ll find providers ranking from clueless private investigators with flashlights, to government-level specialists with over $100,000.00 worth of instrumentation. Cost of instrumentation, by the way, is not always an indicator of effectiveness. Anyone with money can purchase TSCM instrumentation. Knowledge and depth of experience are the primary determining factors to keep your eye on when looking for a competent TSCM consultant.
Take the time to choose your consultant carefully. You may only get one chance to catch an eavesdropper or economic espionage spy. Inferior inspections will miss the bugs, leaving you in a more vulnerable position than you started. You’ll be less cautious. “A false sense of security is worse than a healthy sense of caution.” A competent TSCM inspection will pay for itself many times over.
Since nine out of ten TSCM technicians did not ‘graduate’ in the top 10% of their class, it pays to do your homework first. This is serious business, you need the most competent TSCM consultant you can find.
Tip #2: A website link to a CV or resume is a good clue you have found a TSCM consultant of substance.
Follow these search steps to find the right ONE.
1. Identify a Competent TSCM Consultant worth interviewing.
- Ask a corporate security director to recommendation a competent TSCM consultant.
- Professional association membership directories, like iapsc.org, are also helpful.
- Avoid general business directories. Free listings do not attract quality practitioners.
- Avoid security providers who appears to be a ‘jack-of-all-trades’. By definition, they will not be competent TSCM specialists.
- Avoid providers who also sell security products, or take commissions from sales. Competent TSCM consultants only sell their knowledge and skills. This assures the security recommendations they provide are in your best interest, not theirs.
- Avoid paid search ads. Competent TSCM consultants have long term clients and obtain new clients through referrals. They don’t need to pay for them.
2. Interview a Competent TSCM Consultant.
- Contact your list of candidates and explain your concerns.
- Advise them you have a formal interview process to facilitate a fair comparison.
- Initial requests…
— Have them answer a written list of questions (sample below), with a written response. (This may later be used to document any misrepresentation.)
— Ask them to explain, in writing, what they do. (This part also tests their written communications and organizational skills; especially important because their final report needs to be informative and court-worthy.) The Murray Associates Inspection Protocol™ appears below for comparison.
— Ask them to explain, in writing, their search process and how each type of instrumentation is used.
— Ask them to explain, in writing, their counterespionage philosophy. “I find bugs and catch spies,” is not a philosophy. It is a demonstration of ignorance and shortsightedness. A philosophy is a thoughtful, well-reasoned understanding of ones craft and goals.
— If practical, you may want to meet with your candidates, in person or via teleconferencing. Doing so you will help you gauge their presentability and assess your level of rapport.
3. Asking the Right Questions Helps Determine a Competent TSCM Consultant
- Is Eavesdropping Detection and Counterespionage Consulting your only business?
- How many consecutive years have you been in this business?
- How many years under your current company name?
- Have you ever been sued?
- Has your license ever been revoked?
- Have you ever be disciplined by a licensing agency?
- Have you ever been arrested?
- How many electronic eavesdropping audits have you completed?
- Are your recommendations independent and unbiased?
- Do you profit in any way from your recommendations?
- Can you provide copies of your Certificates of Insurance?
- Do you maintain a full-time staff? How many? What positions?
- Will you provide resumes for yourself and all of your technical staff?
- Do you and your technical staff also have security and corporate investigations experience? If so, please elaborate.
- Are you and/or your staff professionally certified (CPP, CFE, CISM…)?
- Are the certifications ISO recognized? Are they current?
- Have you taught corporate counterespionage on a university level?
- Have you published anything? If so, provide details.
- Do you have meaningful references we can contact?
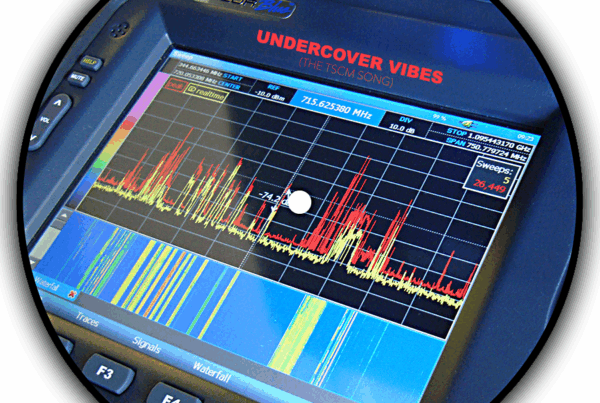
- What is the value of the instrumentation you will bring on premises?
- Will you allow your findings to be verified via polygraph testing?
- Are you qualified to assist with other types of leaks and security matters? If so, describe these other areas.
- Have you ever testified as a court-accepted expert witness?
- Is the majority of your instrumentation classified by the manufacturers as their government/military versions?
- Can your instrumentation test and decode digital VoIP phones?
- Describe the wireless LAN (Wi-Fi) inspection part of your testing process.
Ask about their inspection methodology. Look for a holistic approach to the information security process. Information losses occur via non-electronic surveillance means, too.
4. Before You Say, “You’re Hired.”
If you think you have found the right firm to handle your assignment, great. Time for trust, but verify…
Credibility – Check references, license, insurance, professional certifications, and expert witness status. Think ahead, would this person make a good expert witness for me?
Background – While checking the validity of the license, ask if there are any citations, complaints, or suspensions.
Letter of Engagement – Obtain a signed a Letter of Engagement which clearly defines the assignment. You may also want to add a prohibition against illegal conduct. Mention liabilities, indemnification and remedies if appropriate.
Confidentiality Agreement – A non-disclosure or confidentiality agreement to prohibit sharing of information gathered while on your assignment. It should also include a prohibition against them mentioning the engagement to others, or using your business name for advertising purposes.
Monitoring – Get agreement that: someone representing your interests will be allowed to be with them while they work. Additionally, it provided the opportunity to ask questions, and understand the instrumentation and procedures being used (at appropriate times and outside of the areas of concern, of course).
Reporting – Decide upon an appropriate work product (oral or written), and to whom it will be delivered. Delivery to the General Counsel or outside counsel, with the written report marked privileged and confidential, is recommended. Occasionally a TSCM inspection develops into a legal case, so make sure your consultant would be willing to submit a signed affidavit, describing under oath their work and findings, and they are willing (and qualified) to testify if necessary.
Generally speaking, here are the next steps in the inspection process…
A Competent TSCM Consultant’s Inspection Checklist:
1. The Pre-inspection discussion.
- Determine the reason for this inspection.
- Are there specific concerns?
- Review of problems or suspicious incidents occurring prior to arrival.
- What are the client’s desired expectations and goals?
- Assessment of the assignment with recommendations for a successful completion.
- Orientation and familiarization with the area.
2. The Technical Surveillance Countermeasures (TSCM) inspection.
- Aural – audio listening devices.
- Visual – covert video cameras.
- Communications – telephone, fax, and teleconferencing wiretaps.
- Computer – peripheral data logging and eavesdropping devices.
- Data – other office equipment interceptions.
- Vehicular – GPS tracking, audio and visual surveillance.
- Acoustical leakage, optical loopholes, and other technical surveillance vulnerabilities.
3. An Information Security Survey while on-site to identify alternate information-loss loopholes.
- Non-electronic espionage attacks (dumpster diving, human engineering, etc.).
- Procedural vulnerabilities (unsecured paperwork and keys, unlocked desks and file cabinets, use of wireless presenter’s microphones, posted passwords, ineffective key control, etc.).
4. A Physical Security Survey, to identify:
- Perimeter security weaknesses (inadequate or decayed security hardware, poorly designed alarm systems, etc.).
- Obvious security and safety hazards.
5. An on-site post-inspection debriefing.
6. Submission of a written report within a week to provide…
- Findings and recommendations.
- A list of applicable security resources.
- Certification of client’s proactive information security efforts.
- Counterespionage Compendium of related security vulnerabilities which might be encountered in the future, with corresponding precautions and solutions. (Provided as appropriate.)
7. Value-added services.
- Discreet tamperproof security seals on items like phones and USB cables that you can check on yourself.
- A complimentary Spy Cable Detection Kit, data blockers, and webcam covers.
- Complimentary Q&A assistance in-between inspections.
- Complimentary reinspection reminders.
- Expert witness availability.
- Complimentary security resource recommendation and location services.
Knowing what to expect from a competent TSCM consultant makes your selection task easier. This knowledge should also heighten your comfort level about inviting these outsiders on to your premises.
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.