Economic Espionage is no secret.
Corporations are having their pockets picked, big time.
 Corporate espionage, done correctly, is a covert activity.
Corporate espionage, done correctly, is a covert activity.
You are not supposed to realize you’ve been pickpocketed. Yet, the media reports economic espionage stories almost every day.
This is because the successful attacks, which didn’t stay covert, are being reported more often. These reports are an iceberg’s tip, and everyone is on Titanic. It is necessary to protect your company from economic and corporate espionage.
What is Economic Espionage?
According to the Economic Espionage Act (Title 18 U.S.C. §1831), economic espionage is when someone, knowingly steals, or otherwise obtains without authorization, a trade secret, and then uses this trade secret to knowingly “benefit any foreign government, foreign instrumentality, or foreign agent.”
What is Corporate Espionage?
Corporate espionage is also governed by the Economic Espionage Act (Title 18 U.S.C. §1832). This time, the actor is someone who steals corporate information, trade secrets, or other products to “the economic benefit of anyone other than the owner thereof.”
And, as we said before, these attacks happen often. This article in the NY Law Journal gives several examples of what corporate espionage has looked like in the past.
The main purpose of the Economic Espionage Act was to serve as a deterrent to corporate espionage crimes, whether they are designed to benefit foreign governments or other businesses. It helped, and certainly gave the government some teeth in prosecuting the actors, but (as the NY Law Journal summarizes) in 1997 alone (the year after the passage of the Economic Espionage Act), “the FBI arrested, among others, employees at Bristol-Meyers Squibb, Gillette, Kodak and Avery Dennison for the theft of millions of dollars’ worth of trade secrets.”
One can cautiously surmise these silent muggings are pandemic. Competition is the nature of business, and dirty play is the new normal.
You may be in a position to stem the financial bleeding in your business, or at least advise the person who can. The hero who takes action will: increase company profits, allow expansion, and create employment stability.
You may need help from a corporate espionage consulting firm to truly protect your business.
You can get started today. Here’s your plan…
Step 1. Calculate Economic Espionage Losses
Realize dollar losses from economic espionage are enormous and can be calculated. Product-related losses from espionage are the easiest to calculate. Here’s the formula…
Unrealized Profits = Product Profit x Sales Life Span, in years. (UP = PP x SLS)
Then, add in the cost of…
- research & development,
- tooling for manufacturing,
- marketing, promotion and advertising,
- sales department personnel time,
- invested employee talent in the project,
- legal actions during product development,
- legal actions once the espionage has been discovered,
- stockholder disappointment, and possible law suits,
- loss of consumer goodwill, and potential future purchases,
- the cost of the unsold goods, transportation, warehousing, etc.
Intellectual property and business strategy thefts can be calculated in a similar fashion.
The “UP” numbers are BIG. A calculated loss from only one incident makes a compelling argument for adding a Corporate Espionage Strategy to any security program.
Step 2. Customize a Corporate Counter Espionage Strategy
Successful corporate espionage sometimes pops up as “interesting coincidences,” look-a-like products, and mysteriously lost profits. Most often, it just happens, and nobody can prove espionage for certain.
Every organization needs to think strategically about protecting its assets. Guards, alarms, and locks protect physical assets. Protecting intangible/intellectual property and privacy takes a concerted corporate counter espionage strategy.
In public companies, not having a strategy is indefensible from a stockholder’s point-of-view.
Use this checklist to customize a strategy for your organization.
Corporate Espionage Strategy Checklist
- Obtain management leadership to promote the overall effort.
- Create written guidelines, policies, and enforcement rules for:
— Classification of Documents
— Information Security
— Cybersecurity
— Recording in the Workplace (audio, video & data)
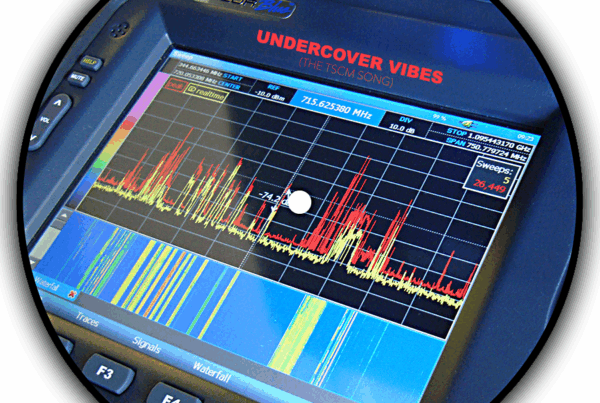
— Technical Surveillance Countermeasures (TSCM / debugging sweeps)
— Area Access Control
— Perimeter Security
Note: There are excellent security consultants who can help you with these tasks. - Provide employee education on information security and workplace espionage.
- Institute intellectual property safeguards (physical and data).
- Designate certain areas as business secret areas. Provide elevated security measures.
- Institute legal compliances – The “non” agreements (non-disclosure, non-compete, etc.) for employees, vendors and consultants to sign.
- Conduct marketplace monitoring for espionage violations.
- Create proactive audit schedules for…
— TSCM audits to detect electronic spying while it is still in the intelligence collection “no harm done yet” phase.
— Wi-Fi audits to identify rogue devices and document compliance with applicable privacy laws (usually conducted during TSCM inspections).
— Information security surveys (usually conducted during TSCM inspections).
— Physical security surveys (often conducted during TSCM inspections).
Create in-house systems to…
— Evaluate employee reports of espionage suspicions.
— Research “interesting coincidences” and look-a-like products.
— Account for the actual and potential dollar value of espionage.
— Create an annual cost / benefit analysis of the counterespionage effort.
Step 3. Institute a Schedule for TSCM Inspection Surveys
Economic espionage intelligence is collected quietly long before it is actually used. The damage isn’t done until they use your information against you. Electronic surveillance is a key component of pre-attack intelligence gathering. It is also the one early-warning sign which is easily detectable.
Periodic inspections help…
Fight
- Competitive Intelligence
- Internal Intrigue
- Strategy Spying
- Media Snooping
Solve
- Mysterious Leaks
- Espionage Problems
- Privacy Invasion
- Eavesdropping Concerns
Protect
- Sensitive Communications
- Trade Secrets
- Boardroom Discussions
- Mergers & Acquisitions
- Delicate Negotiations
- Lawsuit Strategies
- Employee Safety
- Vulnerable Off-site Meetings
- Executive Residences, Home Offices and Corporate Apartments
- Corporate Aircraft, Limos and other transport
- Personal Privacy
- Limit windows-of-vulnerability.
- Identify new vulnerabilities.
Satisfy
- Fiduciary Responsibilities
- Due Diligence Requirements
- Business Secret Status for Court
Increase
- Employee respect for information security.
- Effectiveness of established security measures.
Frequency of TSCM Inspections
For most businesses, TSCM inspections are a quarterly practice. Semiannual and bimonthly schedules are the next most common. Consistent scheduling is as important as the inspection itself.
TSCM Inspection Locations Checklist
- Business offices
- Boardrooms
- Conference rooms
- Private dining rooms
- Executive homes & home offices
- Subsidiary and satellite locations
- Off-site meeting locations
- Company cars, boats, planes.
Budgeting
Determine what percentage of your company’s value is comprised by its intangible assets (intellectual property, goodwill, etc.). In most cases, these assets will be more valuable than the physical assets.
Divide the security budget accordingly between these two groups. The full cost of Technical Surveillance Countermeasures (TSCM) surveys can usually be funded by simply correcting the alignment of the existing security budget.
Pressure to protect easily seen physical assets, and over-spending on IT security, are common problems.
IT security is a very important part of protecting proprietary information. However, keep in mind most of the information in the IT Department’s care was/is available elsewhere in other forms (conversations, meeting notes, etc.) – long before being reduced to computerized data. Spies know this.
Additionally, some of the most valuable information, e.g. strategies, direction-changing decisions, visionary ideas, etc., is never reduced to data.
From an economic espionage point-of-view, the freshest information is the most valuable information. This is why Technical Surveillance Countermeasures (TSCM) surveys are such an important component of the corporate counterespionage strategy.
Let’s Be Blunt
Having a Corporate Counterespionage Strategy these days is an imperative. Not having one is just negligence, and shows poor business sense.
If a Counterespionage Strategy is part of your security program, review it for completeness, and competence. If you don’t have on, create one. Until you do, your company is the weak prey on the business savanna. You will bleed.
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.