Basic bug sweep methodology in business and government.
 It reflects the most commonly-used bug sweep procedures and instrumentation, as practiced by Murray Associates. Your particular concerns, location, security goals and types of communications systems will determine the specific procedures and instrumentation required to conduct a thorough inspection at your location.
It reflects the most commonly-used bug sweep procedures and instrumentation, as practiced by Murray Associates. Your particular concerns, location, security goals and types of communications systems will determine the specific procedures and instrumentation required to conduct a thorough inspection at your location.
The search process is designed so that inspection techniques and tests overlap each other in effectiveness. This automatically creates a system of double-checks.
PRE-INSPECTION DISCUSSION
Before the inspection commences, it is important to understand why it is being done.
- Is this bug sweep pro-active?
- Was there a suspicious incident?
- What are the concerns?
- What are the goals?
- Which areas will be inspected?
This understanding will help the technical team focus their attentions where it will do the most good. This is similar to talking with a doctor, and assures the proper tests will be applied to cure your problem.
THE INSPECTION PROCESS
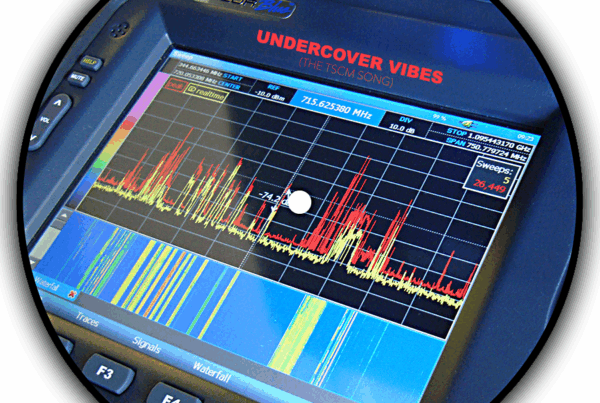
Technical Surveillance Countermeasures (TSCM) Survey
A search of the sensitive areas is conducted using a variety of specialized instrumentation to discover…
- Audio listening devices
- Covert video cameras
- Telephone, fax, and teleconferencing wiretaps
- Computer data logging and eavesdropping devices
- Data and other office equipment interceptions
- Vehicular GPS tracking, audio and visual surveillance
- Acoustical leakage, optical loopholes, and other technical surveillance vulnerabilities
Additional bug sweep tests and search techniques are available for use case-specifically.
Tamper Detection
Discrete tamper proof security seals are used to seal telephones and other objects after they are opened for inspection and testing. This assures that the items have not been tampered with since the last inspection. Items previously inspected and sealed may be re-examined by our clients at any time, to verify seal integrity. A missing seal is also a suspicious incident which should be investigated by the corporate security department, or a competent private investigator. It may indicate the item has been swapped for a bugged one.
Information Security Survey
This phase of the bug sweep is conducted concurrently with the Technical Surveillance Countermeasures (TSCM) operation. It identifies alternate information-loss loopholes such as:
- Non-electronic espionage attacks (dumpster diving, human engineering, etc.).
- Procedural vulnerabilities (unsecured paperwork and keys, unlocked desks and file cabinets, use of wireless presenter’s microphones, posted passwords, ineffective key control, etc.).
Physical Security Survey
The physical security survey is also conducted during the bug sweep. General perimeter security and access control efforts already employed are reviewed to assess both appropriateness, and current effectiveness. Recommendations for improvements, repairs, upgrades, and additions are made as necessary. This phase of the inspection focuses on keeping sensitive areas free from unauthorized access by outsiders.
- Perimeter security weaknesses are identified (inadequate or decayed security hardware, poorly designed alarm systems, etc.).
- Security and safety hazards are noted.
On-site Post-Inspection Debriefing
A full post bug sweep inspection debriefing is provided when appropriate. There are several important reasons for doing this:
- The results of an inspection may want to be known right away by management.
- When electronic eavesdropping or other serious issues are discovered, they may require immediate attention.
- Peace of mind.
Written Report
A written report is prepared to document due diligence and advise others (with a need-to-know) about the bug sweep. A proper TSCM report includes…
- Time and location of the bug sweep.
- Specifics about the areas and communications items inspected.
- Technical attacks and vulnerabilities encountered.
- Security survey observations and recommendations.
- A list of security resources needed to resolve any deficiencies found.
- Information about related security vulnerabilities and foreseeable issues.
A written bug sweep report is also proof of the organization’s proactive information security efforts.
Complimentary Value-Added Services
- Q&A assistance in-between inspections.
- Bug sweep re-inspection reminders.
- Expert witness availability.
- Security resource recommendation and location services.
Our Counterespionage Philosophy
Espionage is a leisurely process. Adversaries quietly collect intelligence long before they use it. Real harm only occurs after the information they collect is used against you. Discover an attack during the intelligence collection phase and you can avoid being harmed.
In business and government espionage…
- Several intelligence collection techniques are usually employed concurrently.
- Eavesdropping is a key component of intelligence gathering.
- Eavesdropping is the espionage tactic which is easiest to detect.
This is why a TSCM bug sweep inspection is the primary security tool used to protect personal privacy and intellectual property.
Regularly scheduled bug sweep inspections are the best way to thwart corporate espionage—during the intelligence collection phase. And, that is what stops your information from being used against you.
For more information, please see:
- Why You Need a Technical Information Security Survey
- How to Choose a Competent TSCM Consultant
- Corporate Counterespionage Strategy – The Basic elements
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.