Wi-Fi Security Audits
 Just one loophole…
Just one loophole…
Hackers are in.
Data is out.
&
“You are out of compliance.”
Wi-Fi Security Audits and Compliance Analysis
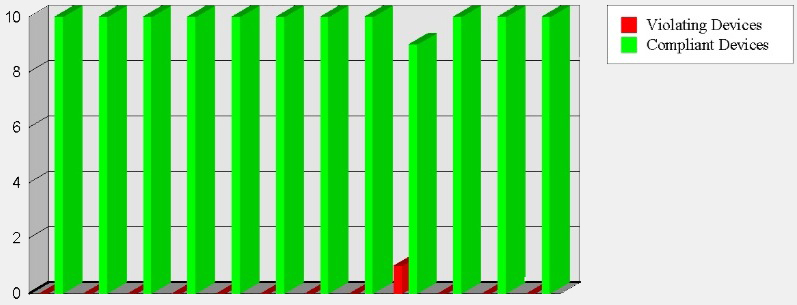
This evaluation includes an examination of how the wireless network security is configured. This is important because it only takes one loophole for hackers to get in, and once they do your data is lost.
Lack of proper network security configuration can create compliance issues; fines are very expensive.
Using TSCM technology, our Wi-Fi Security Audits of Wireless Local Area Networks (WLAN) helps guard against eavesdropping, network intrusions, data theft, and prevent enforcement penalties created by non-compliance to regulations. Our Wi-Fi Security Audits are included as part of our basic TSCM consulting service, but may be ordered separately where compliance is the main issue. This audit is affordable, unobtrusive and easy to schedule.
The following privacy laws and directives may impact your Wi-Fi security.
- Sarbanes-Oxley Act – U.S. Public Companies
- HIPAA – Health Insurance Portability and Accountability Act
- GLBA – Gramm-Leach-Bliley Financial Services Modernization Act
- PCI-DSS – Payment Card Industry Data Security Standard
- FISMA – Federal Information Security Management Act
- DoD 8100.2 – Use of Commercial Wireless Devices, Services, and Technologies in the Department of Defense Global Information Grid
- ISO 27001 – Information Security Management
- Basel II Accord – Banking
Have a Question About TSCM?
If you have any questions about Wi-Fi Security Audits or the TSCM consulting services provided by Murray Associates, simply fill out the form below, or call us from a safe area and phone.
If you think you are under active electronic surveillance, or believe you have discovered a bug or covert video camera, go to our Emergency TSCM page. The procedural checklist there will tell you exactly what you need to do next.
