
TSCM FAQ
Where we take frequently asked questions,
about TSCM and give you clear, concise answers.
Technical Surveillance Countermeasures (TSCM) doesn’t have to be a complicated subject. Even though there is lots of jargon associated with it, it can all be demystified and explained in simple terms. Welcome to TSCM FAQ.
We enjoy acting as technical translators for our clients. Their TSCM questions evaporate as soon as we start talking.
The list below contains some of the most popular TSCM FAQ inquiries we have been asked over the past 45 years.
If you don’t see an answer to your specific TSCM FAQ, please give us a call, or use the contact form at the bottom of the page to receive your answer.
TSCM FAQ 1 - Why do organizations conduct Technical Information Security Evaluations?
• To solve current information loss problems.
• To reveal unauthorized intelligence gathering before a loss occurs.
— This allows time to stop the loss.
— Sensitive information is vulnerable long before it is computerized.
• To protect ideas, strategies, discussions, and intellectual property.
• To limit windows-of-vulnerability.
• To help satisfy due diligence requirements.
• To help satisfy legal and regulatory requirements.
• To avoid non-compliance penalties and fines.
• To help establish the legal status for ‘business secrets’ in court.
• To help protect employee privacy and personal safety.
• To identify new information loss vulnerabilities before they are used against you.

TSCM FAQ 2 - How do we go about using your consulting services?
It’s easy…
1. Contact us from a “safe” area. Tell us about your concerns and security goals. We will provide suggestions and guidance about the best course of action to take.
2. Let us know some information about your security concerns, goals, and the areas you consider sensitive. You may also email us a floor map to help explain.
3. We promptly prepare a written Proposal. It will contain cost-effective pricing (with expenses closely estimated), a suggested inspection strategy, and a Letter of Engagement. There are never any cost surprises when working with Murray Associates. We help you plan your inspection so it stays within your budget.
4. Upon acceptance, we schedule a mutually convenient date for your evaluation. We are available 24/7, at no additional charge.
5. Our team (2-4 persons) will arrive at your location, dressed to blend in, with a few nondescript cases.
6. You are welcome to be with us, and ask questions, throughout the evaluation of your premises. We enjoy explaining what we do.
7. Upon completion, we conduct a verbal debriefing.
8. A full written report is usually delivered within a week. It includes: an executive summary, our findings, explanation of instrumentation and methodology, an inventory of areas evaluated, serial numbers of security seals used, information security vulnerabilities discovered, and cost-effective recommendations for remediation. We are always available to review your report with you. With Murray Associates, your due diligence is documented in writing by an independent and certified, professional security consultant.
9. Once you are a member of our client family, we remain available as your security resource. “Call here first,” whenever you have a security-related question, or need to locate a security resource.
TSCM FAQ 3 - Do you need to see our location before you give us an estimate?
It is rarely necessary to inconvenience you – or tip your hand – with a preliminary visit. Just let us know your security concerns and goals. Use our Details Sheet to assist you. It is the last page of our Introductory Booklet. If your assignment is extensive please include a floor plan.
TSCM FAQ 4 - Do you have references?
After four decades of consulting on eavesdropping and espionage, we have some very impressive references.
• 375+ of the Fortune 1000 companies.
• 800+ others from every imaginable corner of business.
• Located in 38 states, and several foreign countries.
• Many North American government agencies.
Visit our Client Testimonials page for recommendations from our clients. Ask your associates and colleagues about us. Chances are very good we have already helped a security director, or an investigator you know personally. They are our very best references. We can also arrange for you to speak directly with our clients.
TSCM FAQ 5 - What is included in a TSCM evaluation?
This is probably the most often asked TSCM question. The following is a rough outline of what we do during an on-site survey.
Radio Frequency Spectrum Examination
Radio transmitters are the most common eavesdropping devices in use today. Room and telephone bugs transmit audio; spycams may transmit both audio and video. Computer data and keystrokes may also be transmitted out of the area, wirelessly. The Radio Frequency Spectrum Examination is a core component of eavesdropping evaluations. When budgets do not allow full surveys as frequently as you would like, a Radio Emissions exam economically provides an interim level of security.
Wireless LAN Security Audit & Compliance Examination
This exam determines if your system is open and easily available to hackers, intruders and eavesdroppers. It also detects rogue Access Points, innocently placed by employees, or deliberately by an outsider.
Compliance issues under these laws are also discovered:
• Sarbanes-Oxley Act – U.S. Public Companies • EU – CRD (Cad 3) – EU – Capital Requirements Directive
• HIPAA – Health Insurance Portability and Accountability Act • ISO 27001 – Information Security Management
• GLBA – Gramm-Leach-Bliley Financial Services Modernization Act • Basel II Accord – Banking
• PCI-DSS – Payment Card Industry Data Security Standard • FISMA – Federal Information Security Management Act
• DoD 8100.2 – Use of Commercial Wireless Devices, Services, and Technologies in the Dept. of Defense Global Information Grid
Sensitive Area Inspection
- Electronic Surveillance
Key areas, such as the Boardroom, executive offices, and conference rooms, receive a full physical and electronic evaluation. Non-transmitting attacks such as: miniature voice recorders; sound extraction via wire, carrier current, infrared, ultrasonic or laser microphones; covert video (spycams); and keystroke loggers are found this way. These devices may be secreted in hollow walls, false ceilings, furniture, fixtures and other common items which have a legitimate place in the room, such as power strips, radios and clocks. This part is conducted with the aid of Non-Linear Junction Detection, Thermal Emissions Spectrum Analysis, additional tools, and manual search techniques.
-
Communications
Every communications device is a potential eavesdropping tool. We fully inspect each one. This includes: phones, speakerphones, fax machines, print centers, video-teleconferencing equipment, and their associated wiring / equipment racks.
Our communications examination is a battery of tests, including:
• electrical measurements;
• radio-frequency emissions and audio leakage detection;
• an equipment room security check; inspection of wiring;
• non-linear junction and frequency domain reflectometry;
• inspection of feature settings;
• USB spy cable testing;
• and when it can be done, an internal visual review to locate foreign devices and circuit modifications.
Upon completion of our exams, instruments are sealed with serial numbered government-level security tape. You may periodically inspect these seals yourself to detect tampering, or an unauthorized swap of equipment.
-
Security Survey
The technical portion of our survey is only part of our service to you. We consider all aspects of information security. After all, if a bug is not found it doesn’t mean that you didn’t have an information theft, or couldn’t be vulnerable to one in the future. We help you become a hardened target.
We do this by reviewing your current information security policies and procedures with you. We look for evidence of poor employee security practices, like posting passwords on computer screens, or not shredding sensitive wastepaper. We inspect perimeter physical security measures. Security hardware that once worked well may now have decayed, thus leaving you with a false sense of security.
Once we have the our evaluation completed and facts collected we make sense of it all in a written report, which includes cost-effective recommendations and resource information. Our independent security consultant report is also proof of your due diligence, should you need to protect your trade secrets in court.
-
Long-Term Care
Once you become part of our client family, we are always here for you. Think of us as your friend in the security business. Got a question, just call. Need some advice or a recommendation, just call. Some of our clients have been with us for between 30-40 years.
TSCM FAQ 6 - We think there is a problem. What should we do until you get here?
Until we arrive…
• Conduct your affairs normally.
• Do not reveal your suspicions to others.
• Limit confidential conversations.
• Keep detailed notes on anything you feel is suspicious.
• Plan a logical next step if an eavesdropping device is found.
TSCM FAQ 7 - How quickly can you respond?
Very quickly.
Emergencies for client family members are handled immediately.
How do you accomplish this?
Companies who have an ongoing relationship with us unofficially agree to be flexible with their regular scheduling when a fellow family member has an emergency. They know that they will receive the same courtesy in return.
Regularly scheduled inspections can be scheduled promptly as well.
TSCM FAQ 8 - Why trust Murray Associates?
- Our technical consultants have verifiable credentials.
- Experience. Four decades, one specialty, same company name.
- Your confidentiality is assured.
- We provide written estimates with cost-effective pricing. No surprises.
- We are licensed (not required, but voluntarily), bonded, and fully insured.
- All our technical consultants have many years of direct experience with electronic surveillance.
- Our personnel have recognizable, professional certifications: CPP, CISM, CFE, CISM, CDPSE, CISSP, CompTIA Security+, MPSC.
- Government-level TSCM instrumentation.
- We don’t borrow instrumentation “from the day job,” or rent it each time.
- We purchase newest and best instrumentation. (Not old eBay surplus gear.)
- Our inspection without destruction methodology.
- Independent. No secret affiliations with products or manufacturers.
- Honest advice. We do not sell the security solutions we recommend.
- We do not accept commissions, or any consideration from security suppliers.
- Our recommendations are made solely in your best interest.
- We have extensive international TSCM inspection experience.
- 97% U.S.A. made instrumentation and technology.
- We are a full-time corporate counterespionage consulting firm.
TSCM FAQ 9 - What areas of the world do you cover?
Murray Associates’ consulting teams travel internationally for their clients on a regular basis. Headquartered in the New York City metropolitan area, travel is quick and easy for us.
Do you have associates in other locations?
Yes. Being in the security industry for over four decades, we have trusted colleagues in several countries. Bonus… These colleagues are not plucked from a directory. We know these people on a personal basis, have visited their offices, and they have visited ours.
We often manage assignments for our clients with multinational locations, supervising our local contacts during inspections. By doing so, we solve many logistics and availability problems – especially true when several locations worldwide require a unified electronic eavesdropping audit program, or simultaneous inspections.
Simple solution…
Have us manage your multinational electronic eavesdropping audit program. Our experience and contacts will save you time, effort, money and frustration.

TSCM FAQ 10 - Do you install eavesdropping equipment?
No, our practice is limited to pro-privacy services.
TSCM FAQ 11 - Do you sell any equipment, eavesdropping or otherwise?
No. We stick to our specialty; securing our clients’ information and privacy.
We do not sell equipment, endorse products, accept secret commissions, gifts or favors from recommended companies or products. Our income comes from clients who pay us for our experience and unbiased knowledge.
TSCM FAQ 12 - Do you offer eavesdropping detection training?
We do not routinely offer a school or seminars for training technical investigators. We do provide training to our clients who require a secondary, in-house TSCM capability.
Our introductory seminar entitled Electronic Eavesdropping & Industrial Espionage at the John Jay School of Criminal Justice in New York City is not currently being offered. College-level texts which include chapters written by us are usually available at amazon.com.
TSCM FAQ 13 - Can you help me with other security matters?
Absolutely.
Our background in general corporate security is extensive. We understand the issues, and we are very good at devising solutions.
Working closely with many forensic specialists, professional investigators and security agencies lets us know “who’s good” when it comes to giving recommendations.
We maintain extensive files on security products. We buy and test many products (with our own money). We know who makes what well, what it does and doesn’t do, and where to buy it at a fair price.
You will appreciate all the free extras we provide, like our “call-here-first” policy. We save our clients from expensive mistakes, wasted effort, and most importantly – time.
If you want one point of contact for your tough security questions, you will love us.
TSCM FAQ 14 - Is My Cell Phone Bugged?
 Concerned about smartphone eavesdropping, hacking, and spyware? You’ve come to the right place. Our clients receive this book (complimentary) as part of our services. It is also available from amazon.com.
Concerned about smartphone eavesdropping, hacking, and spyware? You’ve come to the right place. Our clients receive this book (complimentary) as part of our services. It is also available from amazon.com.
Is My Cell Phone Bugged? Everything you need to know to keep your mobile conversations private — is a new book which explains, in clear language:
• How to tell if your phone has been hacked or bugged.
• How to prevent spyware from infecting your smartphone.
• What to do if your mobile phone is bugged. (And, what not to do.)
• How to catch your spy, and much more.
This is the do-it-yourself smartphone security handbook for the average person.
TSCM FAQ 15 - How often are TSCM re-evaluations conducted?
• Quarterly is the generally accepted business practice.
• Semiannual and bimonthly schedules are the next most common.
• Occasionally people have requirements for monthly audits.
* Eavesdropping Detection and Wireless LAN Security Audits which are not renewed periodically may be interpreted in court as an admission that previously protected information is no longer important.
TSCM FAQ 16 - What areas should be part of an evaluation?
Any place where sensitive information can be heard, seen, or intercepted.
Additional advice…
There is usually no need to “check every last inch.” Although normal and instinctive, “check everything” does not use our talents efficiently, and is not cost-effective. Have us start with the most sensitive areas. Some of our evaluation will cover all your other areas by default; radio-frequency spectrum analysis and Wi-Fi security and compliance analysis, for example.
There is a point where you will say, “If they have not attacked these areas, then the rest of the areas are probably safe.” With this approach, you will not overspend, and you can move quickly to address any other possible reasons for your concern.
Include the following locations when constructing your list…
• Sensitive areas.
• Adjacent areas, if sounds from sensitive areas can be heard there too.
• All communications equipment within both types of areas (phones, speakerphones, video teleconferencing, faxes, modems, LANs, etc.)
• Devices used for sensitive matters but located elsewhere (mobile teleconferencing, etc.)
• Equipment which handles sensitive printed materials (photocopiers, scanners, A/V equipment, etc.)
• Equipment rooms, wire closets, and junction boxes.
• Transportation vehicles. (cars, planes, boats)
• Off-site meeting locations.
• Corporate apartments or suites.
• Executives’ home offices.
• Company field locations, subsidiaries, etc.
• Other items or areas unique to your organization.
Rules of thumb…
• In sensitive areas, both the room and all communications equipment should be inspected.
• In adjacent areas, both the area and all communications equipment should be inspected if audio from the sensitive area can be heard there.
• Upon rare occasion, communications items may be part of an evaluation without being in the main areas of interest. The reverse is never true.
TSCM FAQ 17 - What are the benefits of having an effective counterespionage strategy?
• Increased profitability.
• Intellectual property protection.
• An environment secure from electronic surveillance invasions.
• Advance warning of intelligence collection activities (spying).
• Double check the effectiveness of current security measures and practices.
• Document compliance with many privacy law requirements.
• Discovery of new information loopholes before they can be used.
• Help fulfill legal the requirement for “Business Secret” status in court.
• Enhanced personal privacy and security.
• Improved employee moral.
• Reduction of consequential losses, e.g. information leak sparks a stockholder’s lawsuit, or activist wiretaps damage good will and sales.
TSCM FAQ 18 - I think I found a bug! What should I do?
This is one of those TSCM questions we hope you never have to ask.
Recently, one of our clients found a bug (in-between our regular evaluations).
The device was a small digital voice recorder, with voice activation capability, taped to a wastepaper can in the Boardroom. The Board Meeting was scheduled for the following morning. We responded on an emergency basis, but the eavesdropping device was removed upon discovery. Their case was blown.
This brings up an important point. If you find a bug, what should you do?
These are your First Responder obligations…
1. Do not to disturb the device. It’s evidence.
2. Do not alert the eavesdropper by talking.
3. Secure the area. It’s a crime scene (Use a non-alerting excuse.)
4. Call us quickly from a ‘safe’ area, using a ‘safe’ phone.
5. Document. Write notes. Take photos. Keep a log of events.
6. Notify only people who have a real ‘need to know.’
7. Observe and note unusual behavior by others.
8. Tell all persons involved to keep it confidential.
We will be there to help you as soon as possible to:
• complete the documentation process;
• review for any additional / supplementary devices;
• evaluate the situation;
• answer questions;
• recommend how to identify the eavesdropper.
Murray Associates can also be your expert witness should your case go to court.
TSCM FAQ 19 - May I call you with non TSCM questions?
Whatever your security question, our policy is, “Call here first!“
If we can’t answer it, chances are excellent we know the best person who can answer it for you, and we will point you in the right direction.
E-mail or phone us +1-908-832-7900
Note: Do not, call from, or discuss your concerns within areas which might be under electronic surveillance.
TSCM FAQ 20 - May I use Murray Associates as a Sub-Contractor?
We prefer the term Adjunct Technical Information Security Consultants, but yes, many people sub-contract our TSCM consulting services.
• Private Detectives
• Attorneys
• Security Firms
• Other Business Consultants
• Meeting Planners
We have a four decade track record of making our business colleagues look like heroes to their clients. We will do the same for you.
Just introduce yourself and we will send you our free white paper…
“The Security Provider’s Guide to Discussing TSCM with business, government and at-risk individuals” (17 Pages)
It will help you explain our TSCM consulting services to your clients, and details why it is smart and profitable for you to partner with us.
Whether you are technically inclined or not, after reading this, you will be able to intelligently discuss these important services with anyone who seeks your advice.
TSCM FAQ 21 - What was your most unusual... ?
Most unusual assignment locations
The middle of the North Atlantic aboard a luxury cruise ship.
Most unusual client
A secret facility that creates serious spy gadgets, and their covert enclosures, for the government.
Most unusual circumstances
An ousted televangelist is publicly accused by his successors of eavesdropping on them. The truth, they were eavesdropping on him.
Most unusual and successful counterespionage assignments
We caught a group of foreign nationals actively engaged in a spy mission in our client’s headquarters. Our client was a Fortune 100 company. They had been diligent over the years in conducting proactive inspections. This day it paid off.
TSCM FAQ 22 - What else should I know about Murray Associates?
Scary is not professional. We don’t have spy vans, mirrored sunglasses or hokey doctor smocks. We arrive at your location as simply ordinary visitors with a few plain cases.
As invited guests to your premises, we always act accordingly. Low key in demeanor, dressed to blend in. We do not disrupt the normal flow of business, or appear out of place after-hours.
We work at your convenience. This means evenings, weekends and even most holidays… at no extra charge.
You can trust our estimates. No nebulous guesses. No surprises.
Our findings can be entered as evidence in legal proceedings. We will also act as your expert witness.
TSCM FAQ 23 - What is the secret to successfully combating economic espionage?
Look for the easiest-to-spot warning sign… electronic surveillance.
Intelligence collection is a leisurely process. Your conversations and information are collected – in many ways – long before they are used against you. Until this intelligence is used, no harm is done.
During the intelligence collection stage you still have time to protect yourself… if, you let us look for the warning signs:
• bugs,
• wiretaps,
• spycams,
• GPS tracking,
• eavesdropping,
• micro voice recorders,
• Bluetooth tracking tags
• GSM cell phone bugs,
• Wi-Fi network intrusions,
• computer keystroke loggers and the traditional espionage techniques.
TSCM FAQ 24 - Do other corporations sweep for bugs?
Yes. Most organizations integrate TSCM security surveys into their overall security program. They protect themselves because…
1. The world has changed. Corporate Espionage is the new Honest Competition. The key to survival is Operational Privacy.
2. Eavesdropping technology is inexpensive. Anybody can do it, and the chances of getting caught are very slim.
3. Many of our communications technologies contain features which allow eavesdropping.
4. General Counsels are concerned that not addressing this security issue would be viewed as negligence by stockholders.
TSCM FAQ 25 - My company wants me to explore in-house TSCM. What should I do?
This is one of those TSCM questions with some variables.
The final answer depends on the situation. Please visit this page for our best advice.
TSCM FAQ 26 - How often should we be conducting TSCM evaluations?
• Quarterly is the generally accepted business practice.
• Semiannual and bimonthly schedules are the next most common.
• Occasionally people have requirements for monthly audits.
Note: TSCM evaluations which are not renewed periodically may be interpreted in court as an admission that previously protected information is no longer a business secret.
TSCM FAQ 27 - Will you help us create a counterespionage strategy?
Yes, in three easy steps.
Evaluation
Our initial inspection of your location includes: an interview to learn about your organization’s culture and concerns; a technical evaluation to discover illegal electronic surveillance activities; and a pro-active information-security evaluation.
Remediation
We will make cost-effective recommendations to make your organization a less attractive target.
Vigilance
Periodic re-evaluations:
- assure new attempts at electronic surveillance are caught quickly, before harm is done;
- discover new loopholes before advantage is taken of them;
- allow testing of security measures already in place, thus assuring continued effectiveness.
In between visits, we are here as your security consultant.
TSCM FAQ 28 - Can I add TSCM protection without increasing my security budget?
TSCM questions like this at first seem unrealistic, but we have an answer…
Sure. The money is probably there; it’s just allocated incorrectly.
Many security budgets are lopsided. They morph out of shape over time. Common causes include pressure to protect the easily seen physical assets, and over-spending on IT security.
You want to avoid a situation where 80% of your budget protects only 20% of your assets. Keep in mind, intellectual assets are far more valuable than physical assets. Evaluate what makes your organization valuable. Then adjust.
TSCM FAQ 29 - Should I worry about Laser Beam Eavesdropping?
This is one of those TSCM questions which we’ve been asked since the 1980’s.
The answer is probably not. Read our guide on laser spying to learn why.
TSCM FAQ 30 - How much business espionage is really going on?
No one really knows. Eavesdropping, wiretapping, snooping, voyeurism, and espionage are covert activities. When done correctly, there is no awareness.
We do know that these activities take place. Stories about spying appear every week in the news media. But, consider this… These stories are actually the spying failures! The successes escape notice.
Even though no one really knows how much bugging is going on, we can logically say, “What we know about is just the tip of the iceberg.“
TSCM FAQ 31 - What does a spy look like?
This is one of the great TSCM questions of all time.
What does a Spy look like?
While there is no exact answer, a composite picture was developed by the Business Espionage Controls and Countermeasures Association…
• 21-35 years old. Female as often as male.
• College graduate with a low-value degree.
• Broad, short-term employment background.
• Money problems – low pay, poor self management.
• Military intelligence experience.
• Acquaintances with law enforcement backgrounds.
• Considered an outsider or loner.
• Disability precluding a law enforcement career.|
• No police record prohibiting sensitive employment.
• Has driver’s license, possibly a poor driving record.
• Romantic hobby / interests …writer, photographer, sky diver, scuba, etc.
• Collects underground & paramilitary literature.
• An active interest in firearms, often with training.
• Recruited from a want ad for Investigative Trainee.
• Often just a drone of a professional handler.
• Skills associated with code breaking and espionage. (music, chess, math, etc.)
Keep this list in mind, but remember…
Your snoop could be anybody.
TSCM FAQ 32 - What are some of the other odd names for bug sweeps?
Many monikers are used to describe TSCM and the people involved.
• TSCM – Technical Surveillance Countermeasures, Technical Surveillance, Counter-measures, Technical Surveillance Counter Measures.
• EECS – Executive Electronic Countermeasures Services, Electronic Eavesdropping Countermeasures Services.
• ECM – Electronic Countermeasures, Electronic Counter Measures.
• EDA – Eavesdropping Detection Audit.
• Anti-bugging – Commonly used in advertising by equipment sellers.
• Bugger – Buggist (UK)
• Bug Sweep – Bug Sweeper, Bug Sweeping, Sweep.
• Countermeasures – Espionage / Electronic Countermeasures.
• Detection – Electronic Eavesdropping Detection, Electronic Surveillance, Detection, Bug Detection, Bug Detecting, Wiretap Detection.
• Electronic Exterminator – Exterminator, Extermination.
• Espionage – Counter Espionage, Espionage Countermeasures, Industrial Espionage, Business Espionage.
• Spy Busting – Spy Busters, Spybusters.
• Surveillance – Counter-Surveillance, Surveillance Countermeasures, Electronic Surveillance Detection.
• Technician – Technical Investigator, Sweeper, De-bugger, De-buggist (UK), Exterminator, Electronic Countermeasures Professional, Counter-surveillance Technician.
If you hear of any others, let us know and we will add them to the TSCM questions list.
TSCM FAQ 33 - Why is eavesdropping, espionage and snooping flourishing?
Factors Promoting Electronic Surveillance
• Risk level: Low.
• Reward level: High.
• Motivators:
— Money.
— Power.
— Sex.
• Eavesdropping Tools:
— Inexpensive.
— Readily available in spy shops and on the Internet.
— Untraceable when purchased from foreign countries.
Other Factors…
• Eavesdropping and espionage used to be morally acceptable in only some cultures. Times have changed.
• Increased competitive pressures placed on employees, consultants and businesses force ethics bending.
• Media glorification presents spying as sexy and justifiable.
• Since the 1960’s, spy toys and games have been actively promoted to children as being fun and acceptable. Children grow up—with no aversion to spying.
TSCM FAQ 34 - Why will the spying problem worsen?
Because we glorify spying to our children. The proof is historic…
“In becoming accustomed to such toys and the pleasures they bring, the seeds of an amoral and suspicious adulthood are unwittingly being cultivated.” — Gary T. Marx
From The Los Angeles Times, December 25, 1988.
As valid today as it was then.
Another insightful article…
Our Snoopy Pups — Charles McGrath, The New York Times
“Which comes first, our passion for surveillance or all the spy toys American kids learn to love? … Far and away the creepiest new toy theme, though, is snooping…”
We consider this the saddest of the TSCM questions.
TSCM FAQ 35 - I think the government is tapping my phone. What can I do?
Not much, and we can’t help you.
But you might want to read…
WHAT HAPPENS WHEN THE U.S. GOVERNMENT TAPS A LINE
The Google AI answer is a good primer.
TSCM FAQ 36 - "Does the company logo have a meaning, or is it just a nice design?"
The Story of the Murray Associates Logo
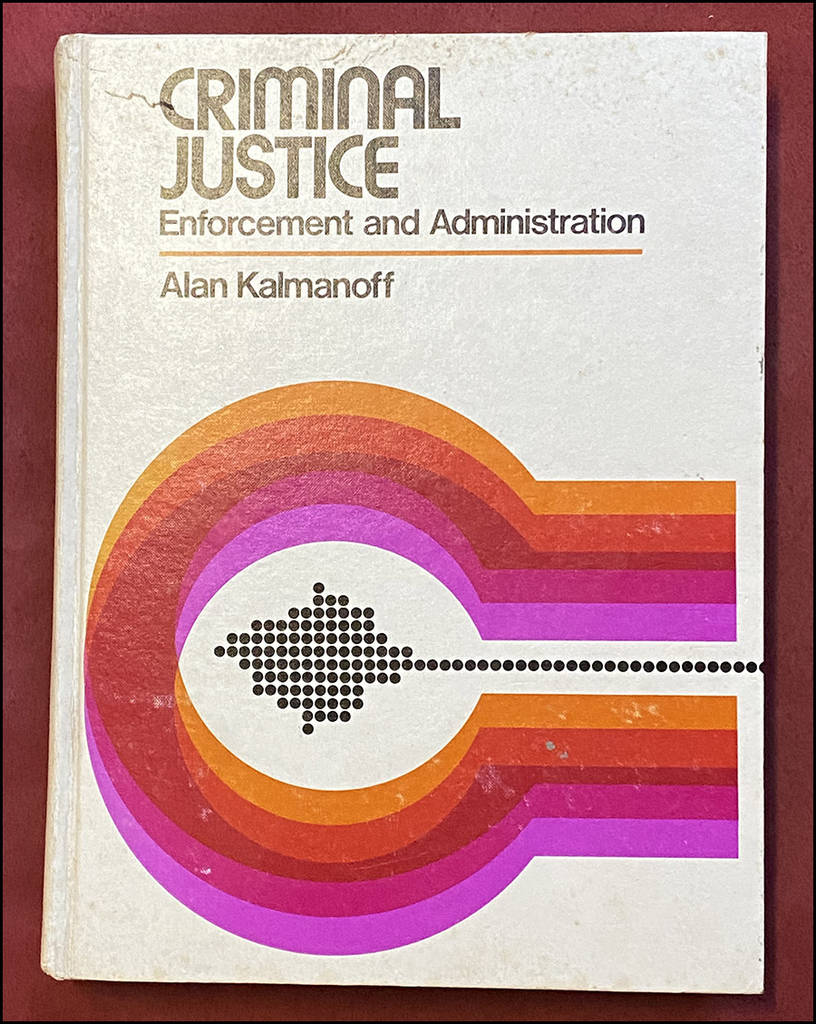
C. 1980
“Does the logo have a meaning, or is it just a nice design?”
The logo does indeed have meaning. It was inspired by my college textbook.
I saw the dots as information in motion, and the rings as protection.

- Blue dots are information.
- The red ring is protection.
- The gray ring represents the many unknown forces trying to steal the information.
Simple… and not inspired by a department store, shooting targets, or a brand of cigarette. Just my design inspired by a book which taught me a lot.
Another reason the shape is appealing is that circles represent comfort, safety, warmth—exactly how I want to make our clients feel.
The logo seems counter-intuitive for a security consulting firm. It goes against the norm… sword, shields, lightning bolts, birds of prey; symbols seen in most security logos. People forget, strong and harsh symbols are used by governments. They are meant to inspire warriors and intimidate enemies. My clients are not enemies.

The way we use the logo behind the company name is also intentionally symbolic, in a subliminal way. It’s the “rising sun” look; used to invoke that upbeat feeling you get when your problems are solved… sing-a-long and sing-a-long some more. ~Kevin D. Murray
Have TSCM FAQ?
If you have any TSCM questions not answered here, simply fill out the form below, or call us from a safe area and phone.
If you think you are under active electronic surveillance, or believe you have discovered a bug or covert video camera, go to our Emergency TSCM page. The procedural checklist there will tell you exactly what you need to do next.
