Securing cryptocurrency offices is a hot topic. Electronic surveillance (the spying kind) has a new target, digital assets.
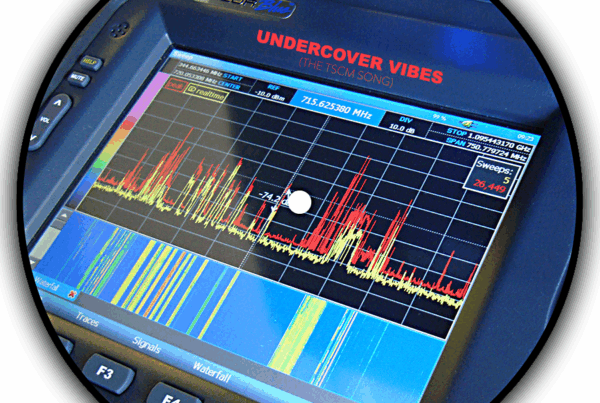
You would be forgiven if you put all the blame on computer hacking. It is a common misconception. Lax security around the office and failing to conduct Technical Surveillance Countermeasures (TSCM) inspections precedes computer hacking. It is the reconnaissance gathered at this stage which allows some hacks to eventually happen. In the case of a crypto currency trading firm, major losses can occur without a hack.
Consider this, leaked strategy conversations can net an eavesdropper millions of dollars before the targeted trader even touches the keyboard. Bugs and other types of eavesdropping devices capture their strategies, as they speak. Valuable words and ideas are zapped away at the speed of light. The IT security folks never had a chance.
TSCM information security inspections actually take a holistic view of information security. At this level of risk multiple information loss vulnerabilities are considered. In short, TSCM is counterespionage for the business world.
 In addition to a trader’s own crypto-assets, their clients’ bespoke portfolios are also at risk. Some cryptocurrency offices also need to protect their cold storage areas. Cold storage is a temporary transfer to an offline wallet. These wallets are kept on devices such as a USB memory stick, CD, hard drive, paper, or offline computer. Then they are stored in safes or hidden locations. This is one reason why detection of covert spy cameras is part a TSCM inspection when securing cryptocurrency offices.
In addition to a trader’s own crypto-assets, their clients’ bespoke portfolios are also at risk. Some cryptocurrency offices also need to protect their cold storage areas. Cold storage is a temporary transfer to an offline wallet. These wallets are kept on devices such as a USB memory stick, CD, hard drive, paper, or offline computer. Then they are stored in safes or hidden locations. This is one reason why detection of covert spy cameras is part a TSCM inspection when securing cryptocurrency offices.
Traders want assurance they are not being spied upon. With crypto market capitalization reaching nearly $2 trillion recently it is no wonder. The cryptocurrencies and crypto derivatives markets are volatile enough without having to worry about financial espionage.
How to Secure a Cryptocurrency Office
- Contact a competent technical security consultant.
- Explain your current security measures, concerns, and goals.
- Conduct an initial TSCM inspection to benchmark the current security posture.
- Review the findings and recommendations with your consultant.
- Create a security remediation plan for the cryptocurrency office.
- Conduct regular follow-up TSCM inspections to limit windows-of-vulnerability should an eavesdropping device(s) be found, and to identify new vulnerabilities. Quarterly inspections are the norm. Less sensitive areas may be scheduled on a triannual or biannual basis if the budget is limited.
Securing cryptocurrency offices with scheduled TSCM bug sweeps is rapidly becoming a standard practice. A sweep team’s written report documents the effort and shows due diligence on the part of the crypto firm.
TSCM counterespionage bug sweeps are cheap insurance. No… better than insurance. Insurance can’t prevent a loss.
Murray Associates TSCM inspections began securing cryptocurrency offices and data centers in 2014, and all other types of businesses since 1978.
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.