Confidential Paperwork Spills the Secrets
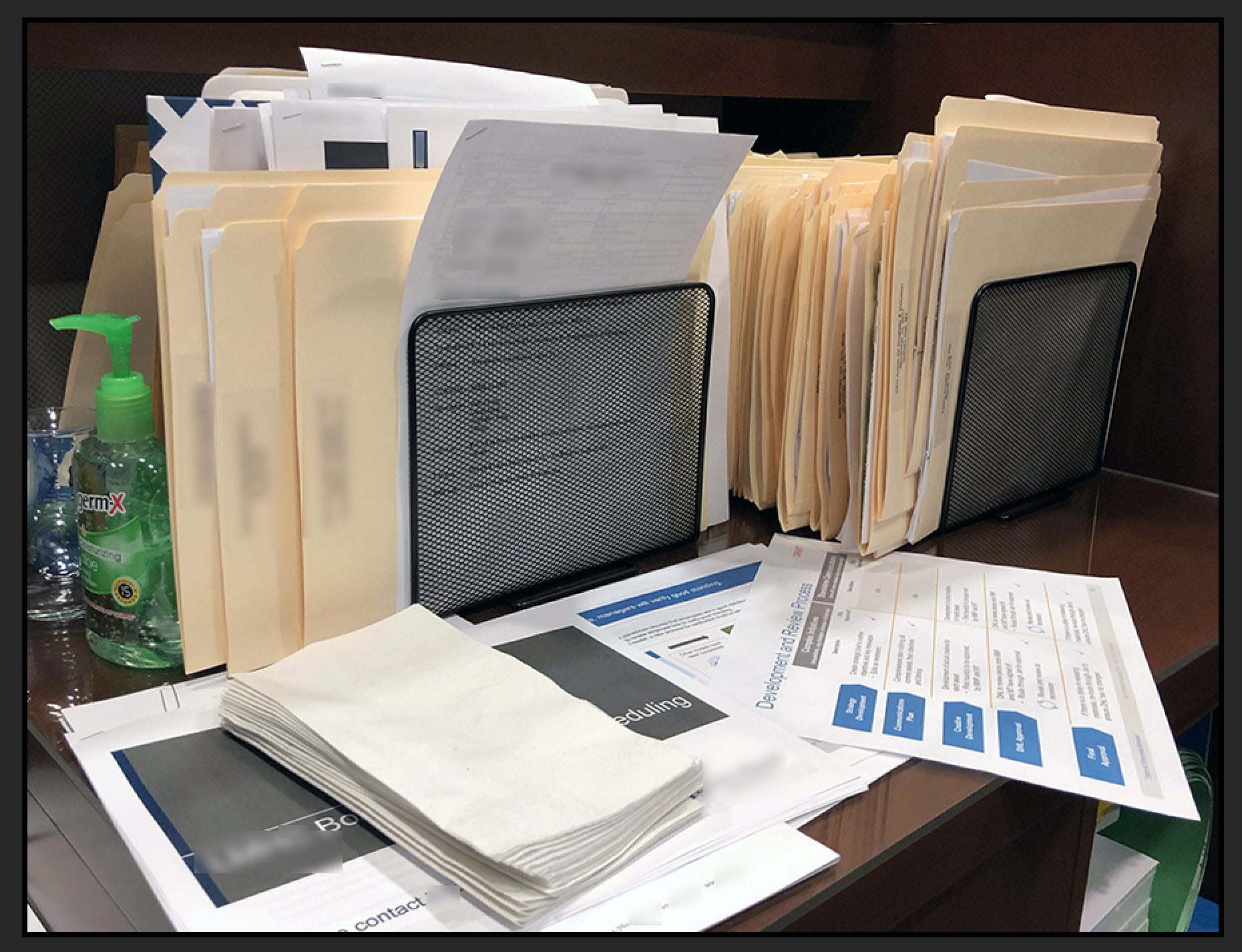
Want to know what’s happening? Read the unsecured confidential paperwork. Employee snoops and after-hours visitors are well aware of this common security breach. They’ll target:
- unshredded trash,
- post-meeting paperwork abandoned in conference rooms,
- folders languishing on desktops awaiting signatures, or processing,
- items left in and around faxes, printers, and copiers.
- and information conveniently pinned to cubicle walls.
These are some of the freshest secrets. Confidential paperwork stored in unlocked desks and file cabinets is next on the list.
Confidential Paperwork Checklist
- Create guidelines for securing sensitive paperwork. They should define what sensitive paperwork is, and the protection rules.
- Make one of the guidelines a Clear Desk Policy. Back it up by providing employees with a secure storage solution (see next section).
Note: Stock locks on most desks and file cabinets will not thwart a concerted espionage attack. These inexpensive locks are easily picked open.
Tip: Most office desks and filing cabinets can be easily retro-fitted with high-security locks.
- Another important guideline is a secure key rule. Keys should not be stored in the same area as the locks they open, like the admin’s desk drawer. Storage in a locked desk, or “a good hiding spot,” is not acceptable either. Spies know about “good hiding spots” and how to pick open simple desk locks.
- Post signs in conference rooms reminding meeting participants to properly secure or dispose of meeting materials. Provide a crosscut shredder in meeting rooms where confidential discussions are held.
Second best: Provide a good quality shred bin which is emptied for shredding regularly. - Check all conference areas for meeting materials left behind. This should be done on a daily basis by a trusted employee. Collected materials should be safely stored or shredded.
- Always escort all non-employees while they are on your premises.
Clear Desk Policy – Confidential Paperwork Storage Solutions

Edsal – 36 in. Keyless Electronic Cabinet by Edsal $351.99

Follow Me 1 – $1,045.00 — Follow Me 2 – $1,450.00

Pro-Stak MAXI, Flat Top Trolley with Digital Pin Code Lock. Two Plastic Coated Metal Shelves & Adjustable Dividers.

SANDUSKY LEE – KDEW3012-05 Wall Mount Storage Cabinet by Edsal $140.71

The Lester Mobile Ped
Cubicle By Design

The Lester Mobile Ped
Cubicle By Design

TENDO – A wide selection of roll-front doors. The range includes both horizontal and vertical roll-fronts.

IKEA – GALANT
Top Lock

IKEA – GALANT Drawer unit/drop file storage, black-brown $169

Supplier: Daskonzept (Designarchiv) & Lista Office
This last suggestion is a bit esoteric. 

Aktentransporter by Ueli Biesenkemp.
It is being used by one of our clients in Switzerland and caught my eye while working there. Basically, it is two bookcases, on wheels, and hinged like a clamshell on one side. Every executive assistant has one conveniently located behind where they sit. It has an excellent lock, holds a lot, looks good, and is easy to use.
High Security Locks for Confidential Paperwork
If you want to continue using existing desk and file cabinets for confidential paperwork storage you can replace the low-security locks with high-security locks. You have two choices. Either use high-security keyways, or use combination locks. Some electronic combination locks could be seen on the cabinets in the previous section. An interesting non-electronic version appears in this section.
Keep in mind the information in this post applies to most average organizations. Government and high-security facilities needs require more sophisticated hardware.
Kenstan Lock Company is a manufacturer of high-quality showcase and cabinet locks. They manufacture five comprehensive lines of showcase and cabinet locks, each with its own specialized security level for retail, commercial and Industrial use.

Kenstan also offers a wide range of door hardware locks including mortise and rim cylinders, as well as, lever and tubular handles for fitting rooms, stock rooms and offices.

Wesko – Radical Disc Cam Lock

Medeco – Cabinet Locks

FMJ – High Security Cam Locks
“The innovative EVO/EVO+ system is suitable for everything that you would like to keep under lock and key inside your furniture (cabinets, lockboxes, etc.). Only persons whom you have provided with the code have access. The EVO/EVO+ design meets all the requirements. You need to retrofit existing furniture? Nothing could be easier. (VIDEO)
The EVO/EVO+ can be integrated easily into standard lock cut-outs. Thus, retrofitting is that easy. Remove the core. Insert the BeCode EVO. Done! The “+” in EVO+ means: The EVO comes with an integrated cylinder lock. Retrofitting this system into an existing cabinet is as simple as child’s play: Remove the old cylinder lock. Insert the EVO+. Done! There is no other electronic lock that can be retrofitted that easily.”
RFID Locks – Electronic furniture locks can be both invisible and simple to operate.

RFID chips can open the lock through up to 25mm of wood or glass. One manufacturer claims up to 30,000 cycles per battery, or… the lock can be opened more than nine times a day for over 10 years. Fulterer Camden Eproer
Unfortunately, not all confidential paperwork is easy to secure.
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.