Evolution of the Spy Generation
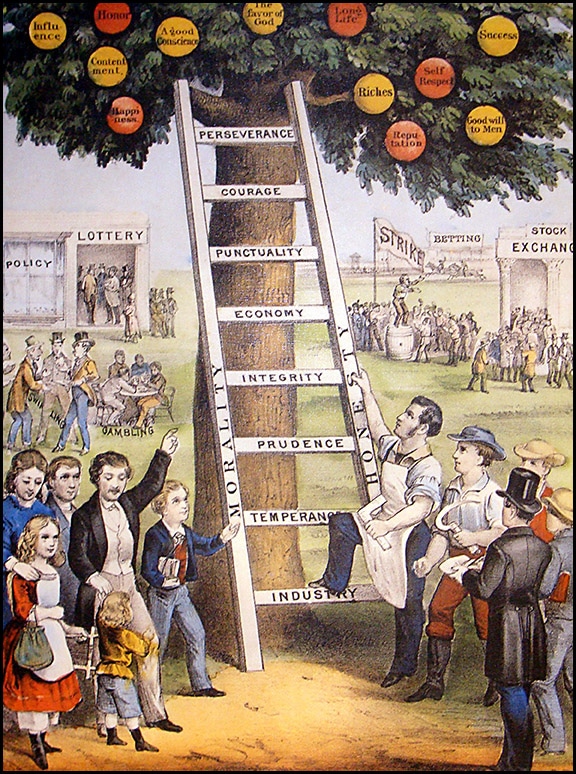
Spying as a method of getting ahead in business, was not encouraged in days gone by. Children were taught entrepreneurial ideals, like: hard work, independence, persistence, and inventiveness.
So, how did we get to…
“Screw it, let’s spy!”
An Evolutionary Process
Seasoned readers will remember the days when kids had heroes who exemplified moral codes: The Shadow, Joe Friday (Dragnet), Dan Matthews (Highway Patrol), The Lone Ranger, etc.
Others may remember the glamorization of the “good” spy from TV shows like: Secret Agent, The Man from U.N.C.L.E., Mission Impossible, I Spy, and The Prisoner.
These entertainments still languish deep in digital tombs like YouTube—as forgotten as the Greek Chorus. On the bright side, at least these morality plays still exist.
1960’s spy shows spawned a huge market for children’s spy toys. The market remains strong today, and the toys are much more technically advanced.
Children have grown up with spy toys for decades. Spy toy makers blatantly promote spying as cool and fun. Eventually this propaganda becomes truth.
The morally strong TV heroes children used to look up to have disappeared. The “Super Hero” genre of today has little connection with the past. The good vs. evil dividing line in their plots are fuzzy. The super heroes themselves are perplexed. Dark sides and cracks in morality infect the genre. “Golly gee, Superman. What happened?” (J. Olson, 1955)
Several generations of children are now desensitized to spying. So now, as adults, some of them have moral compasses that look like Batman fidget spinners.
Today’s Information Security Reality
Here is a brief excerpt from an Entrepreneur Magazine article I read recently.
—***—
3 Reasons You Should Spy on Your Competition
One of the best ways to thoroughly understand your market is to take a look at your competition. By not spying, you are at a significant disadvantage.
Here are three reasons it’s a good idea to spy on your competition…
- Without spying, it’s impossible to know what you’re up against — as a result, you can’t completely prepare.
- It’s easy to do. Don’t be discouraged from spying on your competition by assuming that it is daunting or resource intensive.
- It would be wasteful to not spy. Speaking of wasted resources, without spying on your competition it’s very easy to waste time trying to find your ideal market and your reach.
—***—
Times changed. The spy kids grew up. You are being targeted.
The workplace is now filled with former children who have no compunction about spying. Twenty percent of them would sell their passwords. Almost everyone has a multipurpose spy tool in their pocket. (Maxwell Smart only had a shoe phone.) And, if one needs a thumb-sized bug that can be monitored from any cell phone in the world… it can be purchased on eBay for less than $25.00.
Analysis of Business Espionage Today
- Risk level: Low.
- Reward level: High.
- Why people spy in the workplace:
– Money.
– Power.
– Sex. - Advanced Surveillance Tools:
– Inexpensive.
– Readily available in spy shops and on the Internet.
– Untraceable when purchased from foreign countries.
Other Factors Contributing to Business Espionage
- Social mores about eavesdropping and espionage have changed.
- Increased competitive pressures placed on employees, consultants and businesses force ethics bending.
- Media glorification presents spying as sexy and justifiable.
- Since the 60’s, spy toys and games were actively promoted to children as being fun and acceptable. Children grow up.
The Biggest Information Security Mistake
“We don’t need a Technical Information Security Survey. We’ve never had a spying issue here.”
Truth… You would not know if you did. Successful spying is invisible.
Spy Rule #1 – Be invisible.
By definition, successful espionage goes undetected, only failures become known. If you ignore business espionage, or decide a “risk-assessment” gamble is a good idea, you will never know when you’re bleeding information. (Parasites don’t alert their hosts.)
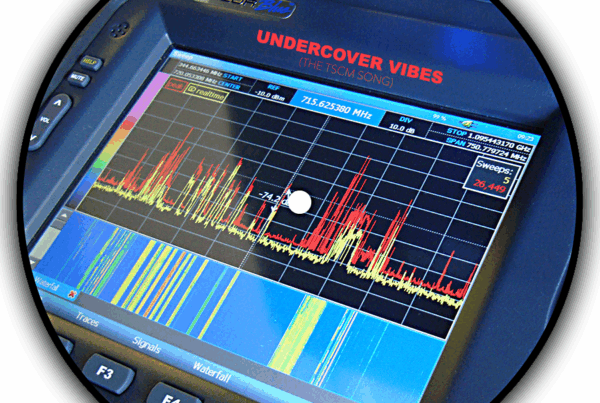
The Solution Spies Hate
The Technical Surveillance Countermeasures Survey which actively looks for:
- evidence of information security failures,
- evidence of electronic surveillance: audio, video and data,
- information loss vulnerabilities in: the workplace, your transportation, your home office, and at off-site meeting venues,
- loopholes in your perimeter security,
- decaying or broken security hardware,
- information security policies no longer being followed,
- and information security vulnerabilities inherent in the office equipment you use every day.
Vigilant organizations conduct these surveys during off-hours, and often on a quarterly basis. Diligent organizations tend to have their information security surveys conducted biannually. Negligent organizations, well, they just have their pockets picked. The point is, re-inspections limit windows-of-vulnerability, and they cost less.
An independent consultant’s report is proof of your organization’s due diligence. It will also help prove the enhanced duty-of-care, required for protecting trade secrets and other sensitive information in court.
Considering what is at stake, a Technical Information Security Survey is very economical insurance.
No, it is even better than espionage insurance… it can prevent losses in the first place.
Add it to your information security program.
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.
v.190105