Q. How often do you find bugs or other surveillance devices?
 A. There are two types of Technical Surveillance Countermeasures (TSCM) inspections used to find bugs: business and government-level sweeps, and residential sweeps for private individuals. The find rate depends on the type of sweep.
A. There are two types of Technical Surveillance Countermeasures (TSCM) inspections used to find bugs: business and government-level sweeps, and residential sweeps for private individuals. The find rate depends on the type of sweep.
My firm mainly conducts electronic surveillance detection sweeps for bugs and surveillance devices found in businesses and governments, so let’s start here.
With business and government organizations, the opposition’s focus is on getting hot information, in all its forms. Corporate espionage, industrial espionage, call it what you will. There is no one spy tool of choice used to find bugs. Electronic surveillance plus hundreds of other tradecraft techniques are available for the opposition to employ. The average residential sweep doesn’t need to take this into account. More on that later.
Proactive Due Diligence Sweeps to Find Bugs in Businesses and Governments
Regularly scheduled, due-diligence technical information security surveys rarely uncover electronic surveillance bugs. Do not be surprised. Typically, organizations using these services already have a high overall security profile. They are “hardened targets.” For those clients, the benefits of incorporating TSCM into their security program include…
- Having a known window-of-opportunity when something is found.
- Identifying decayed security hardware which no longer works as expected.
- Identifying security policies which are no longer being followed.
- And, becoming aware of a variety of otherwise unseen security issues.
Emergency Sweeps to Find Bugs in Business and Government
Discovery statistics on our “emergency TSCM sweeps” vary from year to year. These are the sweeps commissioned because electronic surveillance is suspected. We find bugs and other electronic-related compromises in approximately 2% to 5% of these sweeps. The overall success rate in solving these cases, however, is very high. It is just that the answer to most of these emergency sweeps involves non-electronic methods, which we also seek out. These include the following:
- Poor or lapsed security practices.
- Poorly designed, installed, or decayed security hardware.
- Human element: key control, unshredded confidential wastepaper, big mouths, etc.
A holistic TSCM inspection can solve most of these emergency cases, no matter how the loss was incurred.
Solving these organizational emergency cases requires more than a standard TSCM bug sweep. Additional skills and experience required include corporate investigations, alarm system design, computer forensics, and information security management, among others.
Residential Bug Sweeps – Often Find Bugs
When it comes to residential and matrimonial bug sweeps, the find rate for locating bugs and surveillance devices is quite a bit higher. This makes sense. The eavesdroppers’ focus is narrow. They want to intercept:
- conversations and/or video voyeurism images,
- and/or determine the location of a specific person.
Electronic surveillance is the tool of choice, whether it be audio/video bugs or computer/smartphone spyware. Personal privacy is the loss most associated with private individuals, unlike business espionage, where intellectual property is also targeted.
Solving cases for private individuals is relatively easy for the following reasons:
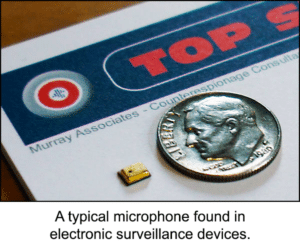
- The spy is usually a do-it-yourselfer, an amateur, or someone with limited tradecraft skills.
- The victim has a good idea who is doing the spying and their capabilities.
- Inexpensive, easy-to-obtain, and easy-to-find bugs are most often used.
- Locations for the placement of bugs, taps, spy cameras, and trackers are limited.
- Having a personal stake in this type of surveillance, spies often reveal their involvement as a display of power.
Private investigators and TSCM providers who handle residential and matrimonial bug sweep cases don’t charge very much for their services. However, the good ones can quite successfully find bugs and GPS trackers. The fraudulent providers simply talk fast, wave a wand, take the money, and run. It pays to interview several vendors and get a few recommendations, before hiring anyone.
The lower-than-corporate fees they charge are due to:
- They have lower overhead for running their businesses.
- Their detection equipment is basic, outdated, or borrowed from their day jobs.
- Their insurance coverage (if any) does not meet corporate standards.
- Their continuing education expenses are minimal.
- They provide no extras, like written reports or information security surveys.
Some of this is understandable. The private individual market they serve can’t support, nor does it need, the sophisticated level of detection required by businesses and government agencies.
Even with these limitations, the honest low-budget-level TSCM inspectors are quite successful. They often find bugs and trackers of the consumer-grade variety.
Business and Government Level TSCM Technical Investigators Who Find Bugs
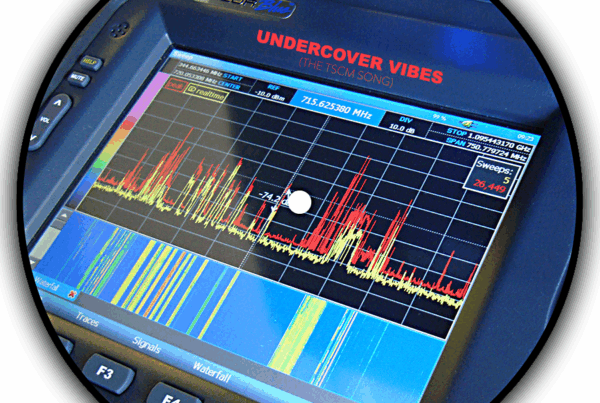
Professional security consultants who specialize in business and government-level TSCM are not a dime a dozen. They invest heavily and continually in: Sophisticated instrumentation, professional certifications, and advanced (and continuous) training. Their overhead includes: an office staff, trained Technical Investigators, licensing, insurance, instrument calibration, and an annual Carnet so they can travel internationally for their clients.
Security directors know the stakes are very high, hence the saying: “It’s not just about the money. It’s about what you get for your money.”
These corporate executives are charged with protecting their corporate assets. This type of information security requires a security consultant with a depth of experience and knowledge of information management, corporate investigations, complex security systems, and yes, high-level Technical Surveillance Countermeasures.
Benefits of Quality TSCM
The two main goals in eavesdropping, espionage, and voyeurism attacks are :
- To obtain the desired audio and/or visual information or raw data.
- To avoid detection.
So, if you do not actively inspect for eavesdropping, espionage, and voyeurism attacks you will not know you are under attack.
Unlike private individuals, organizations do not have a choice about conducting proactive TSCM bug sweeps. Being subjected to theft or information loss is not an option. This is why TSCM is such an important element of their security programs.
The benefits of a Technical Information Security Survey (enhanced TSCM) for organizations include:
- Increased profitability
- Protection of intellectual property
- A working environment secure from electronic surveillance and privacy invasions.
- Advance warning of intelligence collection gathering (espionage).
- Evaluates the effectiveness of current security measures and practices.
- Documents compliance with applicable privacy law requirements.
- Discovery of new information security vulnerabilities, before they can be exploited.
- Assists in fulfilling legal requirement for “Business Secrets” status in court.
- Enhances personal privacy and security.
- Improves employee morale.
- Reduces of consequential losses, such as information leaks that can spark a stockholder lawsuits, activist wiretapping, and damage to “goodwill” and sales.
The list of benefits is much longer, but you get the idea.
There are some excellent private individual and corporate-level TSCM consultants out there. Pick the right one for your needs and it is almost certain that your privacy and security concerns will be resolved in a cost-effective manner. You can begin your search here, or here, or learn more about how to evaluate a TSCM provider, here.
###
Murray Associates is an independent security consulting firm, that provides eavesdropping detection and counterespionage services to businesses, governments and at-risk individuals.
Headquartered in the New York metropolitan area, Murray Associates’ teams can assist you quickly anywhere in the United States and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.