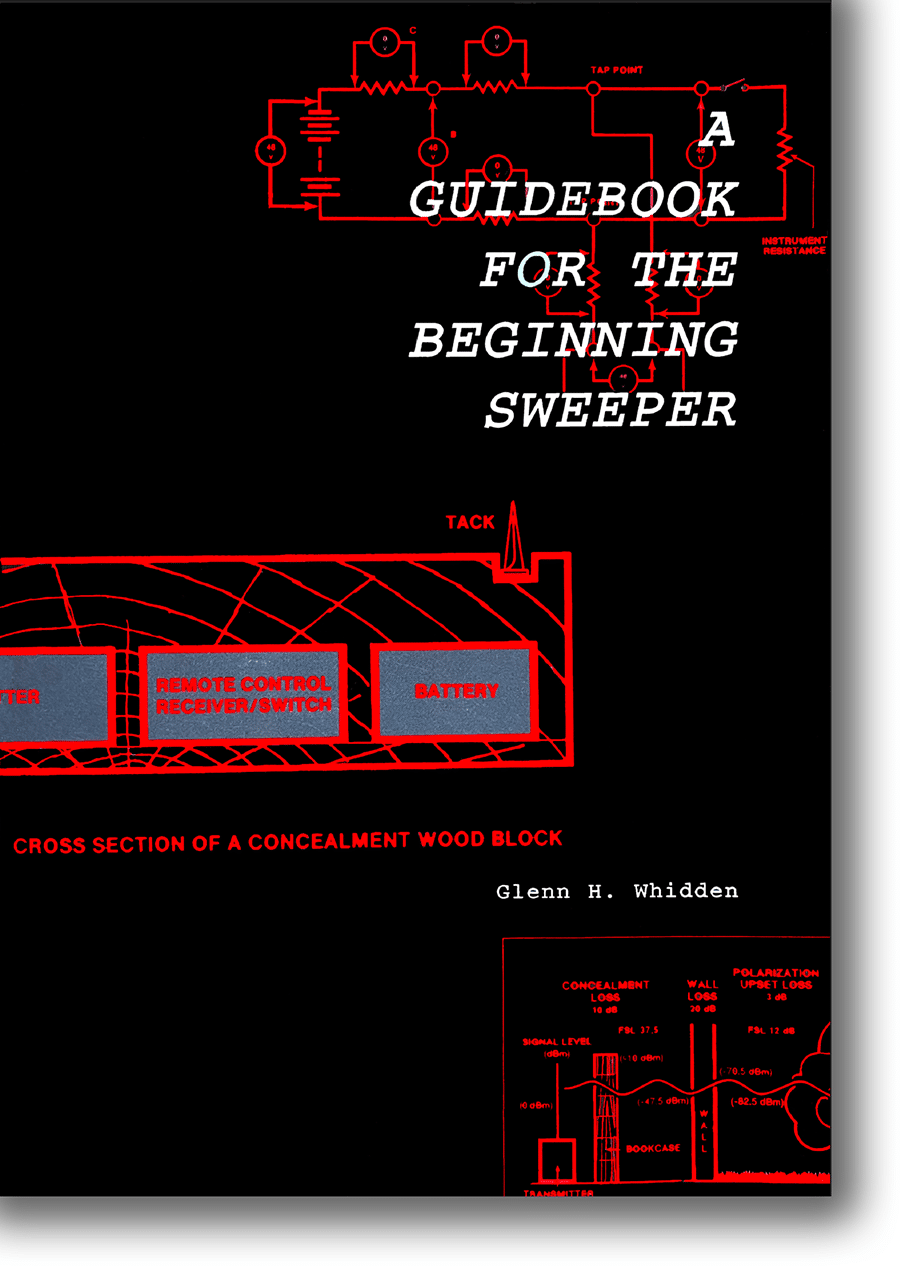
A Guidebook for the Beginning Sweeper, by Glenn H. Whidden, 1994
A Guidebook for the Beginning Sweeper, is an introduction to newcomers to the Technical Surveillance Countermeasures (TSCM) field. Because it is out-of-print and unavailable on the used book market I digitized my personal copy so others may continue to benefit from Glenn’s extensive knowledge and valuable experience.
Although not a full TSCM course, the basics are here. Most of his instruction remains as important today as they did when the book was first published.
The book’s digitized format is a read-only pdf. The cost of the download is $19.95. All fees above the cost of production are available to Mr. Whidden’s heirs. Please use the PayPal logo to submit payment. You will be emailed a download the code within 1-2 business days. Thank you.

A Guidebook for the Beginning Sweeper – FOREWORD
Electronic eavesdropping is one tool of the espionage agent. It is a dangerous and insidious method of penetrating an espionage target. It is dangerous because it can be used to steal secrets that are not accessible in any other way. It is insidious because the victim may never know that his secrets were stolen. Whatever its characteristics, there is a threat to be met.
Some have responded in one way or another. Although it cannot be characterized as traditional, it is certainly true that many people have individually straightened their ties, pulled back their shoulders and proclaimed, “I will be a sweeper”.
Their reasons for making that decision have been varied. Some have heard that the rewards are enormous. Others think it would be fun to do and also rewarding. Some others are attracted by the mystery that is associated with espionage work.
Whatever the reason, they make inquiries and find that sweepers use an X device, a Y device and sometimes a Z device. They also learn that an investment of $Xy will be required to acquire those devices. They find a client who will hire them, purchase the equipment, study the operating instructions and, in effect, are in business.
There are others who, having received expensive government training, go into the sweep business after leaving government service. They acquire the appropriate equipment, hang out a shingle and begin their new enterprise.
And then there are a few who emerge from the halls of academia to engage in the discipline of counter-eavesdropping. They prepare themselves for the engagement through study programs, the acquisition of devices, and the hanging out of a shingle.
In considering these few categories of sweepers, should one be critical and decide that one is better than another? Who knows? This author does not believe so.
For example, should one sneer when he hears it proclaimed that an advanced academic degree is an important pre-requisite for success as a sweeper? Of course not! Certainly, the ‘grunt’ work of sweeping does not call for that amount of formal TSCM education to be effective. Indeed, there have been cases in sophisticated government work where practitioners achieved a high rate of success against a very professional opposition without the benefit of a college degree in anything related to electronic eavesdropping.
It must be added however, that one who is mentally prepared, through the process of a formal education, to recognize and identify symptoms of eavesdropping activity, to analyze them, develop their ramifications and then destroy the effectiveness of the espionage operation and its operator, is potentially of extraordinary value to the security industry. If he also promulgates information on the eavesdropping systems and their vulnerabilities, he could be a shining jewel on the security scene. So far, he has not appeared. It is to be hoped that he will.
The academic who keeps one foot in academia and puts the other forth into the security industry may or may not be educated enough to do the job. The trend seems to be for him to exercise his intellect by studying and commenting on the work of others or through the production of statistical studies on this or that. That work can be very helpful in the overall scheme of things too. It can indirectly hurt the bad guys if the comments and studies are read, understood, and applied by those doing the grunt work.
Foreword Page 2
Now let’s swerve over to contemplate the entrepreneur who has invested in sweep devices but who may only be peripherally experienced or trained as a sweeper. Should we be disdainful? Certainly not! Such a person can find instruction on the details of the eavesdropping threat and how to counter it. He or she can be fully functional and can mentally profit from experience as it is accumulated. A smart, busy and tireless practitioner can do real harm to the bad guys.
Then too, there are those who have stepped into the sunlight of the business world from the obscurity, or cloak and dagger atmosphere of government. Here we have a mixed bag of potential effectiveness. The expenditure of time and money made to train them could have been heavy or light depending on a variety of factors. They may have been exposed to the light of knowledge that is comprised of a distillation of the information gained through the examination of a great deal of opposition activities. Something better than 100 proof should have been the result of the distillation. But it was given a security classification. The result has often been an individual who is sometimes equipped with an expensive haircut, suit and shoes, business facilities that are tastefully furnished, and an air of mystery. Should he be suspected of being a phony or instead be held in high regard because of his aura and the knowledge that he may possess of things classified? Who knows? One cannot make a decision on the basis of superficial observations. One must watch what he does and then judge how effective he is against the bad guys. He could be a real threat to them, but he must also know how to work in the world of commerce and industry. The rules of engagement and conduct are not the same as those in government.
One can see therefore, that sweepers are of a mixed bag. The author can be content, as an observer of the scene, with the preparations and efforts of all the diverse types of people occupied in the defense against electronic eavesdropping. He can be so because he believes that a thoughtful, intelligent and industrious person can become an effective sweeper whatever his former career and education may have been.
Each sweeper should have started from one point however, A Guidebook for the Beginning Sweeper. That is by finding out what eavesdroppers do and what their vulnerabilities are.
Foreword Page 3
Having done that, he or she must have learned the techniques, tests, and devices to employ in exploiting those vulnerabilities. Throughout his career, he must have searched for and devoured any information that appeared anywhere on the subject of eavesdropping. New methods and devices continually appear on the scene.
Then, he must have acquired the equipment for his work and figuratively slept with it until he knew its performance characteristics in intimate detail. There should have been no consulting the instruction book during the course of a sweep. The operation of the equipment should have become second nature. Having done that, he worked out his plan of attack for the different types of situations that he encountered and then went looking for clients.
Now, as time passes, and he gains experience, he will modify and refine his methods and gradually develop a reputation. If that is for honesty, integrity, and effectiveness, he will make a real contribution to the security industry. He doesn’t need to be a genius, a scientist or an ex-spook to start down that path.
It will be noticed that the title of this book, A Guidebook for the Beginning Sweeper, indicates that the “Sweep” is only one element of an eavesdropping defense. That is correct. There are other ways of defending against eavesdropping. If an area in which sensitive conversations take place is not physically protected against hostile installations of eavesdropping equipment, the area could be penetrated at any time. If that condition prevails, a complete sweep prior to each conversation occurring therein will be necessary. As that is usually quite impractical, the element of “Prevention” is an important factor in an eavesdropping defense. That is, penetrations must be prevented to the extent possible.
Another element in an eavesdropping defense is that of “Deterrence”. If the defense is perceived to be formidable to a would-be eavesdropper, he may refrain from attempting a penetration.
On the other hand, if he sees a certain vulnerability, he might be encouraged to exploit it. If that vulnerability was designed by the defender and left in place, it could be used as a trap to detect eavesdropper activity when it begins. If such a process of deception is contemplated, it should be dealt with very carefully because the eavesdropper may perceive things about a situation that another person might not.
In any case, it can be seen that there are at least three elements to an eavesdropping defense. They are, Deterrence, Prevention, and Detection. As the title states, the TSCM inspection or “Sweep”, which is the Detection element, is only one of them. In the absence of the other two, detection efforts can be fruitless. End Foreword – A Guidebook for the Beginning Sweeper
###
Murray Associates is an independent security consulting firm, providing eavesdropping detection and counterespionage services to business, government and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.
EXTRAS:
• More security tips, spy and privacy news at spybusters.blogspot.com. Be sure to sign up for the free email updates.
• Concerned about Spy Cameras? Learn how to detect them.