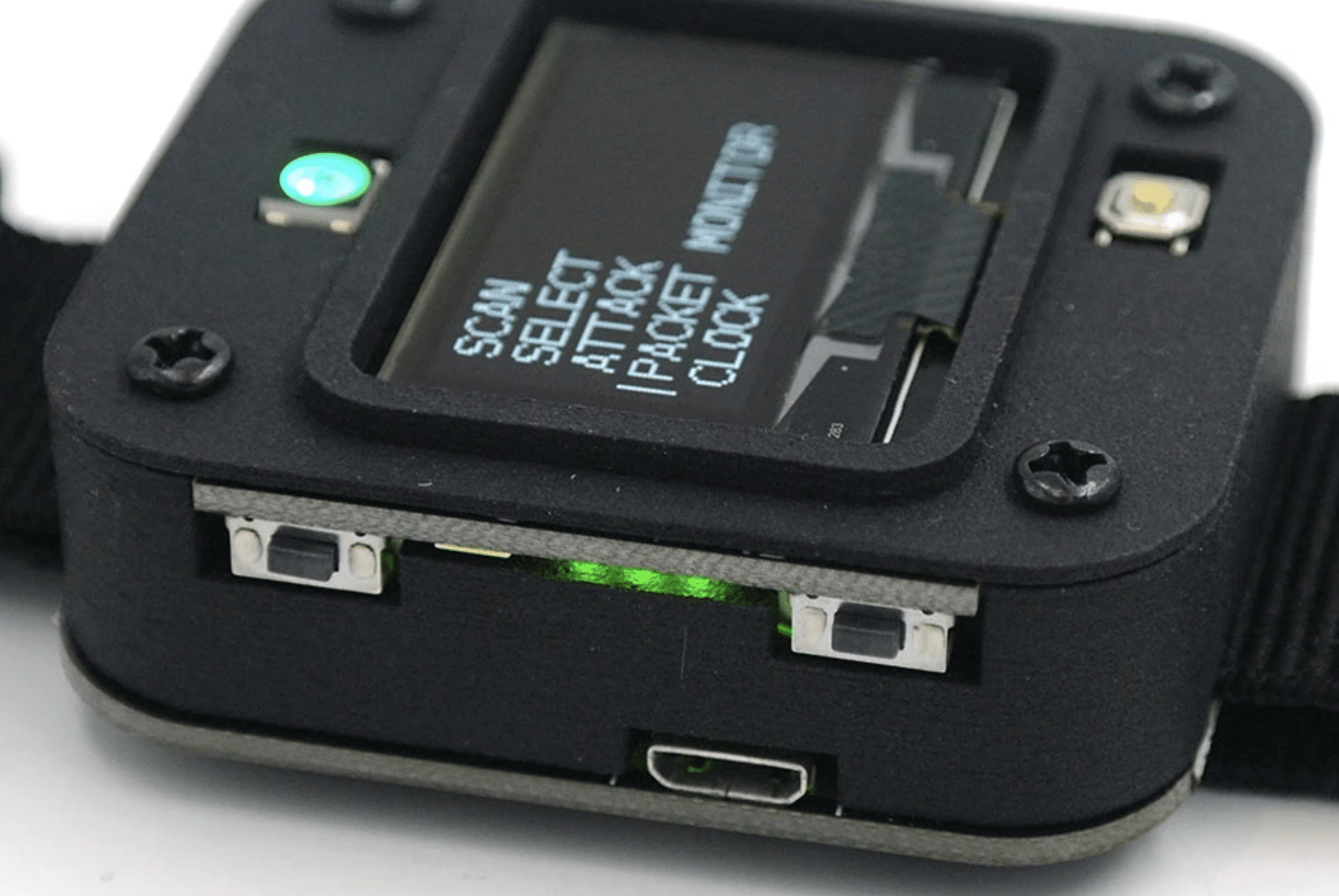
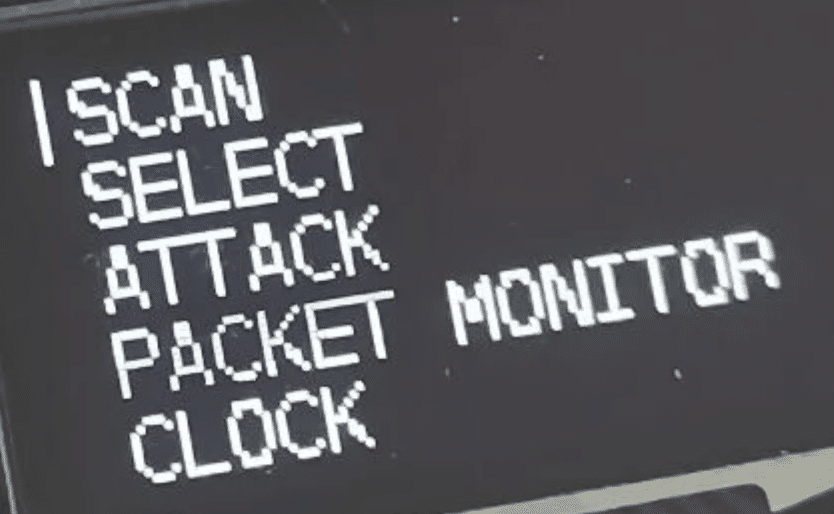
This cheap “watch” is used by hackers and thieves to disable Wi-Fi cameras and other devices. (It has some legitimate uses, too.)
This cheap “watch” is used by hackers and thieves to disable Wi-Fi cameras and other devices. (It has some legitimate uses, too.)
Watch Functions
– Deauther Attack: Disconnect 2.4G WiFi
– Deauther Beacon: Create fake networks
– Deauther Probe: Confuse Wi-Fi trackers
– Packet Monitor: Display Wi-Fi traffic
– Kicks devices off a WiFi network- Spam beacon frames
– Spam probe requests
How Hackers Disable WiFi Cameras
Additional background information about deauthentication attacks via Atlas VPN…
A deauth or deauthentication attack (DoS) disrupts connections between users and Wi-Fi access points. The attackers force devices to lose access and then reconnect to a network they control. Then, perpetrators can track connections, capture login details, or trick users into installing rogue programs… this attack does not need unique skills or elaborate equipment. Deauth attacks could also knock devices offline, like home security software.
How it it Used?
 Forcing hidden cameras to go offline. Over the years, frequent disputes forced Airbnb to forbid the use of cameras in rented apartments or rooms. Yet, more cunning homeowners can conceal cameras from their guests.
Forcing hidden cameras to go offline. Over the years, frequent disputes forced Airbnb to forbid the use of cameras in rented apartments or rooms. Yet, more cunning homeowners can conceal cameras from their guests. - Hotels that push paid Wi-Fi. There have been incidents when hotels employed deauthentication attacks to promote their Wi-Fi services. In fact, the Federal Communications Commission (FCC) issued documents stating that blocking or interfering with Wi-Fi hotspots is illegal. One of the first offenders was the Marriott hotel, with financial motives for disrupting visitors’ access points. However, charging perpetrators with deauthentication attacks is a rare sight. Usually, victims might blame the interruptions on unstable Wi-Fi.
- Susceptible smart devices. Criminals could push connected devices offline for several reasons. One danger is that attackers might disable security systems. Thus, such interruption halts monitoring of the home, office, or another area. In worst-case scenarios, such deauth attacks could facilitate burglars entering buildings. Another example comes from a vulnerability in Ring Video Doorbell Pro (now fixed). The exploited flaw means using a Wi-FI deauthentication attack to force the device to re-enter the configuration mode. Then, eavesdroppers can capture Wi-Fi credentials orchestrated to travel in an unencrypted HTTP.
- Forcing users to join evil twins. Spoofed deauthentication frames force targeted devices to drop their connection. It could be a way to break the legitimate connection and trick users into joining fake hotspots. Deauth attacks could flood the access point so that devices cannot join for a period of time.
Our Tips: How to Make Sure They Don’t Disable WiFi Cameras
Tip 1. Don’t go wireless, use Cat6a shielded cable.
Tip 2. Use Power over Ethernet (PoE). Make sure it is properly grounded.
Tip 3. Make sure the power supply to the network is backed-up (UPS). Power failures do happen.
Tip 4. Hide the cables to deter sabotage.
Tip 5. If you absolutely, positively need a wireless video solution consider using a 4G cellular camera, or a dedicated video link.
WiFi Camera Attack Prevention
The prevention of deauthentication attacks does not offer many options. But there are effective strategies for mitigating their impact. Ensure that your network applies WPA2 encryption. If you use a pre-shared key, it must be complex and lengthy to withstand threats like brute-force attacks. Another improvement might be 802.11w, which validates deauthentication frames and discards spoofed ones. Older hardware and IoT might not support it, raising issues for some Wi-Fi clients.
Furthermore, remember you have minimal control over free public Wi-Fi and its security.
A VPN can assist if deauthentication attacks force clients to connect to evil twins. Atlas VPN creates a secure path between users and access points. Encrypted traffic will prevent attackers from capturing any meaningful communications or data.
###
Murray Associates is an independent security consulting firm, providing eavesdropping attack detection and counterespionage services to business, government, and at-risk individuals.
Headquartered in the New York metropolitan area, a Murray Associates team can assist you quickly, anywhere in the United States, and internationally.